Police in seven European countries have acted to disrupt what it says was among the largest phishing operations worldwide, Tycoon 2FA.
Microsoft
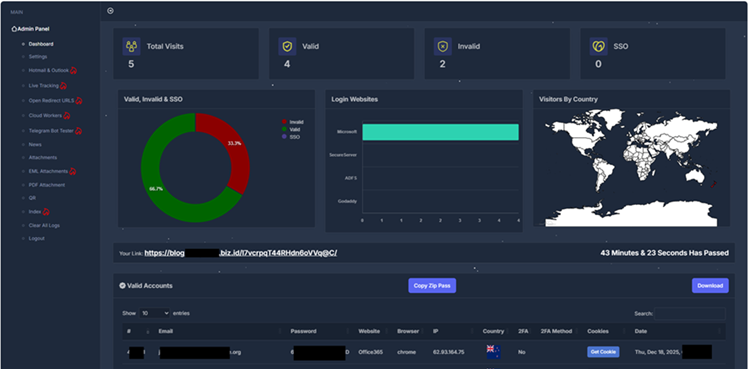
The phishing-as-a-service (PhaaS) operation was active since 2023, with Europol saying that two years later, it accounted for nearly two-thirds of all phishing attempts blocked by Microsoft.
Several technology companies were involved in the takedown, including Microsoft, Trend Micro which shared the intelligence that sparked the initial investigation, Intel471, Proofpoint, Coinbase and the Shadow Server Foundation in UK.
Cloudflare provided a high-level description of how Tycoon 2FA would proxy a real Microsoft 365 or Google login page, which victims would enter their credentials and multifactor authentication (MFA) codes on.
The login details would then be passed onto the legitimate services in real-time, Cloudflare said, but once the session token for identity confirmation was returned, Tycoon 2FA would steal it.
Attackers would then import the session token into their own browsers, to gain authenticated access to victims' accounts.
Tycoon 2FA abused the Cloudflare Workers serverless compute services to act as a sophisticated proxy for login and 2FA requests, the internet infrastructure company said.
The criminals were able to steal credentials and MFA codes for Microsoft, GoDaddy and Okta, Cloudflare said.
It added that the scripts were engineered with rigorous anti-analysis protections to terminate sessions suspected to be watched by security researchers' tools.
With the hijacked session tokens, attackers were able to embed themselves in corporate email environments to monitor internal communications and financial workflows, Cloudflare said.
This, in turn, meant they could send legitimate looking invoices from compromised accounts to third-party partners or vendors, as the message originated from trusted, authenticated sources.
Using FIDO2 and WebAuthn hardware keys such as YubiKeys or passkeys mitigates PhaaS threats such as Tycoon 2FA, Cloudflare said.
Microsoft applied to seize 330 active domains used by Tycoon 2FA at a United States District Court, a method the technology giant has utilised before to disrupt the activities of criminal gangs.
Tycoon 2FA where able to trick an estimated 96,000 victims worldwide, with healthcare and educational organisations the hardest hit, Microsoft said.
Microsoft observed that the Tycoon 2FA operators and the developer of the Raccoon365 PhaaS kit, Nigerian Joshua Ogundipe who was arrested last year, were in contact with each other, indicating a level of cooperation between phishing criminals.
Europol did not indicate that any arrests had been made in the Tycoon 2FA takedown.



_(33).jpg&h=140&w=231&c=1&s=0)
.jpg&h=140&w=231&c=1&s=0)


_(39).jpg&w=100&c=1&s=0)



 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



