That a single fire can take down Telstra services nationwide is pretty bad on its own, but last week's exchange blaze also served us up an important reminder: that we need to stop using texts for two-factor authentication.
While Telstra techies struggled to get the kit set ablaze by the fire back in operation, something went wonky and text messages were delivered to the wrong recipients.
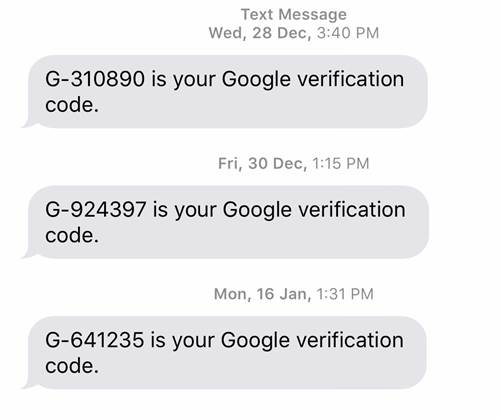
Some of the misfired messages were pretty entertaining - I wonder if this person ever got their peanut M&Ms? - but it gets less funny when you start thinking about how many important services use SMS as an out-of-band channel for challenge and response authentication codes.
We're talking about everything from social networks to internet banking and government services - all of which are targeted by hackers every day.
SMS 2FA is also used to protect email, often the keys to the kingdom given people use their email addresses for login IDs for a vast amount of services.
So needless to say, a lot of damage can be done through a compromised email account, making additional protection with a secondary authentication method not just a good idea, but necessary.
Of course a convenient way to do this is by sending codes via SMS in order to avoid man-in-the-middle interception.
And in its day, it made sense: everyone has a mobile phone and can receive texts without needing any user training.
But it's 2017. SMS has been weighed and found wanting when it comes to security: America’s National Institute of Standards and Technology (NIST) last year saw the writing on the wall and put SMS 2FA on its “to be deprecated” list.
It's not super easy to listen in on GSM traffic and capture the 2FA tokens, but it can be done with a bit of expertise, background information, and patience. So can siphoning off GSM signals.
Hooking up with a rogue telco to abuse the signalling system 7 (SS7) that sets up voice calls and message transmission between subscribers could be worthwhile to capture 2FS SMS in bulk, but that’s probably a bit too obvious especially in the long run.
Malware like Marcher on Android can snag 2FA tokens, which is great because everyone has a phone and many of them are no longer updated by vendors, leaving millions of devices forever vulnerable.
If that’s too complicated, there’s porting of victims' phone numbers, or good old social engineering: a message arrives telling users to expect a text with a code because their account is under attack and needs to be verified, please reply to the message with the code.
Then there’s your telco screwing up message delivery.
That SMS messages went to random people means you should think twice before trusting Telstra’s - or any telco's - network for authentication of your sensitive accounts.
We need to properly start looking to alternatives to SMS 2FA like time-based one-time passwords (TOTP), which generate temporary authentication codes in an app, transmitting nothing over a network.
Taking it further and ditching codes altogether, push-to-accept notifications could work as long as they have multiple, different accept buttons to prevent users from inadvertently allowing logins.
More complex solutions include the FIDO Alliance’s universal two-factor (U2F) USB or NFC keys.
Either way, SMS 2FA has had its day. It's time for it to be put to rest.












 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards












_(1).jpg&h=140&w=231&c=1&s=0)



