Showing that physical access to a device can spell "game over" for its security, a Canadian penetration tester has successfully demonstrated a string of attacks that allow a determined threat actor to get through data protection measures in PCs.
At the annual Hackfest security conference in Quebec City, Canada, Pierre-Nicolas Allard-Coutu detailed elaborate attacks against Windows 10 and 11 PCs.
These succeeded in bypassing multiple security measures that would normally prevent access to stolen laptops and the data they contain.
Such measures include passwords to protect computers' BIOS/UEFI firmware that store important security control settings for direct memory access (DMA).
As the name implies, DMA is a technology that lets peripheral devices directly read and write to system memory instead of going through the central processing unit (CPU) in computers, for better performance.
Allard-Coutu obtained DMA through the use of a Peripheral Component Interconnect express (PCIe) connector to which he connected a field programmable gate array (FPGA) card.
Even then, modern PCs come with a number of security measures to prevent attackers from gaining access; these include kernel DMA protection, input/output memory management unit (IOMMU) to control peripheral access to system memory, Secure Boot, virtualisation based security, and firmware protections.
Another much vaunted security feature is Microsoft's whole-of-disk encryption, BitLocker.
This uses the Trusted Platform Module (TPM) which stores and protects a long master key to decrypt storage as Windows starts up.
Most of the time, TPM will automatically decrypt the storage in a computer and this is what Allard-Coutu focused on: it is a convenience feature for faster startup of PCs for users, but provides weaker security without a second authentication method.
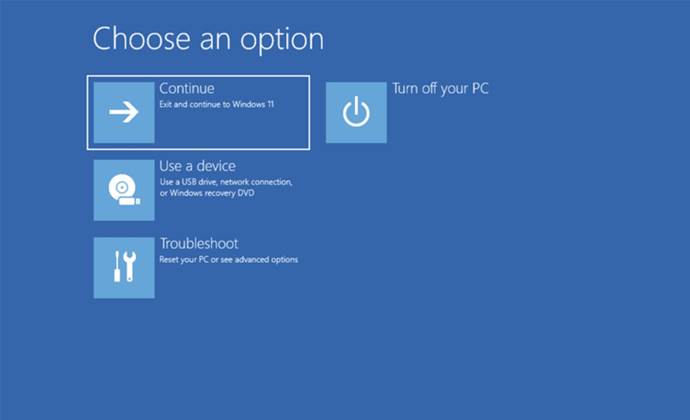
For Windows 11, Allard-Coutu was able to conduct his attack with the Windows Recovery Environment (WinRE) for troubleshooting, which tends to be enabled in most laptops, and which provides command line access.
By using the PCILeech framework, and developing two utilities, DMAReaper and FirstStrike, Allard-Coutu patiently worked his way through the computer's defences, at one stage even copying and modifying BIOS images.
Interestingly, one area of Allard-Coutu's presentation was obscured as it appears to be a zero-day vulnerability that allows an attacker to modify a certain nonvolatile random access memory (NVRAM) variable, which can disable pre-boot DMA protection.
This, without requiring a BIOS password to be entered to change the DMA protection setting.
The vulnerability won't trigger the usual BitLocker recovery, either.
Technical details on the vulnerability are being withheld by Allard-Coutu as it is affecting multiple major firmware vendors currently.
How to harden laptops
Allard-Coutu suggested two relatively easy to implement measures for users and administrators to improve the protection of Windows PCs
First, enabling BIOS/UEFI passwords is worthwhile, as it adds a "speed bump" that considerably lengthens the effort attackers will have to expend to get access to laptops.
Second, Allard-Coutu said not to rely on the TPM solely for decryption of storage, and to add a complex, alphanumeric personal identification number (PIN) as well, a recommendation other researchers have made before.
Doing so would be unpopular as it adds a second, inconvenient authentication step for users, but storage protected with a PIN-enabled TPM would prevent Allard-Coutu's current attacks.
The threat model here features advanced adversaries who are skilled, well-funded and have lengthy physical access to devices, Allard-Coutu said.
Furthermore, the success rate of elaborate attacks such as the above depends on hardware generation and configuration.


.jpg&h=140&w=231&c=1&s=0)








 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 Forrester's AI Forum Sydney
Forrester's AI Forum Sydney
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



