Sydney-based penetration tester Jonathan Brossard has created a hardware backdoor that replaces a machine’s BIOS and is extremely difficult to remove.
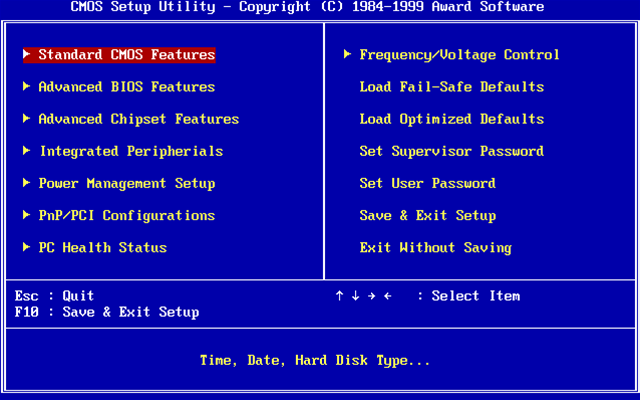
The proof of concept firmware dubbed Rakshasa, named after the mythical demon in Hindu, replaced the BIOS with open source software Coreboot and SeaBIOS and could mimick many boot logos.
It was highly persistent and able to infect firmware in peripheral hardware devices through PCI expansion, plus could load iPXE firmware to the network card.
Once malware had spread to the devices, it could reinstall on the BIOS should the user attempt to reflash the original firmware.
It was designed to download the malicious bootkit files over a variety of internet connections when a system started up. These would be written briefly to memory rather than the master boot record, a tactic that left nothing for forensic analysts to find even in live analysis, Brossard said.
Configuration and version updates could be also downloaded from command and control servers.
Installation typically required physical access to a target machine in order to activate firmware write protection which took the form of an on and off switch on some devices.
The most realistic attack scenario was within the supply chain where a manufacturer could install the malware, but Brossard says remote installation could be possible on a machine already in an attackers’ control that did not have BIOS write protection, and because Coreboot was able to load PCI extension firmware before the stock firmware on the network card.
Brossard did not release the code. More information was available in his technical paper (pdf).




.jpg&h=140&w=231&c=1&s=0)





 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 Forrester's AI Forum Sydney
Forrester's AI Forum Sydney
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



