American Megatrends has attempted to calm rising panic over the leak of the cryptographic signing keys and source code for its UEFI BIOS, the code that starts up millions of computers around the world.
Last week, United States security researcher and penetration tester Adam Caudill received a tip-off from his research partner Brandon Wilson that a Taiwanese vendor had left a file transfer protocol (ftp) server open for anyone to browse and download data from.
Included - among internal emails and other data - were the source code for AMI's UEFI BIOS and cryptographic signing keys used for verification of it.
With access to the source code for the UEFI BIOS and the cryptographic signing keys to verify the final binary programs, the researcers feared that attackers could create and disseminate malicious updates that in turn could be used to compromise and control millions of computers worldwide for a long time to come.
According to Caudill, "this kind of leak is a dream come true for advanced corporate espionage or intelligence operations."
"The ability to create a nearly undetectable, permanent hole in a system’s security is an ideal scenario for covert information collection," Caudill writes.
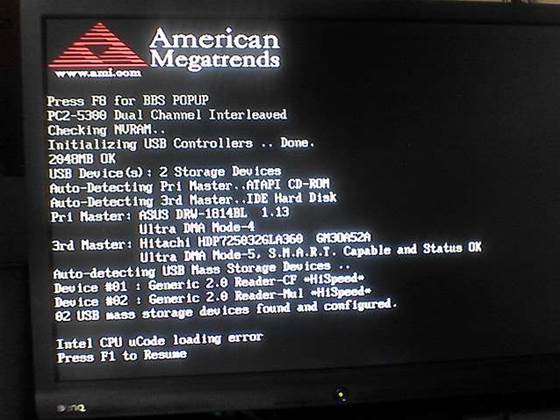
The basic input/output system or BIOS is code stored in non-volatile read-only memory on personal computers and similar devices. It runs when devices start up and loads operating systems, initialising of hardware such as they keyboard, storage and video beforehand.
To overcome limitations of the original BIOS specification - which was designed for 16-bit computers decades ago - and to provide further features such as cryptographic security for booting up, the Unified Extensible Firmware Interface was developed from 2005 onwards.
AMI, which claims to be the world's largest BIOS vendor, said in response to Caudill and Wilson's findings that the security keys on the ftp server were in fact test ones and not used for production systems.
American Megatrends chief executive and co-founder Subramonian Shankar stated that “while today’s news is certainly distressing, AMI would like to reassure its customers and partners in no uncertain terms that this should not be a security concern for them."
"If they follow standard operating procedure for BIOS signing, the security features in our BIOS source code and secure signing process will function as designed and remain 100 percent secure,” Shankar says.
Caudill notes however that while AMI instructs vendors using its UEFI BIOS to change the key before building a production environment, it is not known if the customer with the open ftp server was following that practice.
Caudill did not reveal which Taiwanese vendor leaked the information.











.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



