Security software firm Intego has claimed a spike in infections by an "insidious" variant of a Mac trojan it uncovered last year.
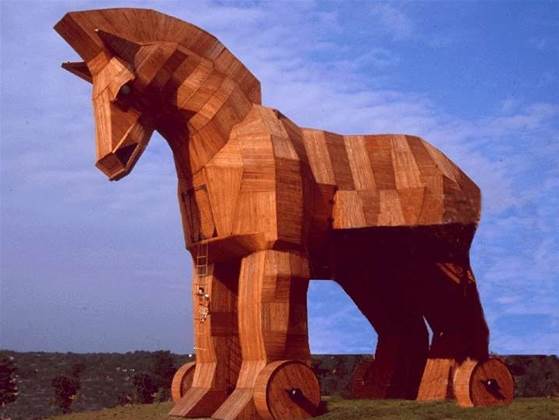
The company posted "evidence" of the infections gleaned from Apple and Skype discussion boards to its blog.
It first revealed the existence of the variants - dubbed Flashback.G - in early February.
Flashback.G requires very little user intervention. It exploits holes in Java vulnerabilities to install the malware on a user's mac computer.
In the event the user has up-to-date Java settings, the malware masks its installation using a social engineering trick, appearing as a digital certificate from "Apple Inc." that needs to be approved.
The malware installs itself in the /Users/Shared folder and comes with a .so extension with various names.
"One of the clues that a Mac is infected is that certain applications will crash," Intego said.
"This is notably the case for web browsers, such as Safari, or other network programs, such as Skype. This is because the injected code interferes with the program making it unstable."
Most cases of infection have been seen on Macs running OS X 10.6 Snow Leopard. OS X Lion does not come with Java installed.
The firm urged users to update to the latest version of Java and not to click on suspicious digital certificate notifications.
It also urged those who had been infected to send Java applet samples to Intego for further analysis.










 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



