
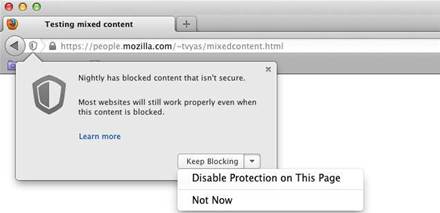
Insecure content served over HTTPS is blocked under the latest version of Mozilla Firefox released hours ago.
The FireFox 23 upgrade closed off an avenue of attack present in previous versions of the popular browser that allowed the loading mixed active content in which unencrypted resources were served up within HTTPS pages.
"... if a HTTPS page includes HTTP content, the HTTP portion can be read or modified by attackers, even though the main page is served over HTTPS," Mozilla security engineer Tanvi Vyas said.
However the threat posed mixed content was not entirely eradicated since mixed passive content like images, video and object requests was still loaded.
That content was a lesser risk than active content because it could not alter the Document Object Model of a webpage, but it could still undermine HTTPS protection.
"... the attacker can observe the HTTP headers sent with the image, including the user agent string and any cookies associated with the domain the image is served from. If the image is served from the same domain as the main webpage, then the protection HTTPS provides to the user’s account becomes useless, since an attacker can read the user’s cookies from image request headers," Vyas said.
If Mozilla had blocked the mixed passive content abundant over the internet, then users would be inundated with security messages defeating protection measures in the long term, Vyas said.
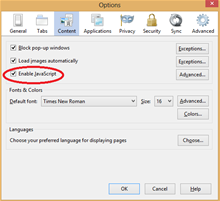
Developers have also removed the checkbox to block JavaScript erasing user preferences and meaning the script would be activated by default when users upgraded to version 23.
Users could block mixed passive content and JavaScript by:
- Opening a FireFox tab and typing about:config in the address bar
- Click through the warning page and change the value of security.mixed_content.block_display_content to true by double clicking it.
- Click through the warning page and change the value of java.enable










.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



