The best-selling servers of Dell are among a swathe of IT products released by US companies that have been compromised by the National Security Agency, information security enthusiasts were told at a conference overnight.
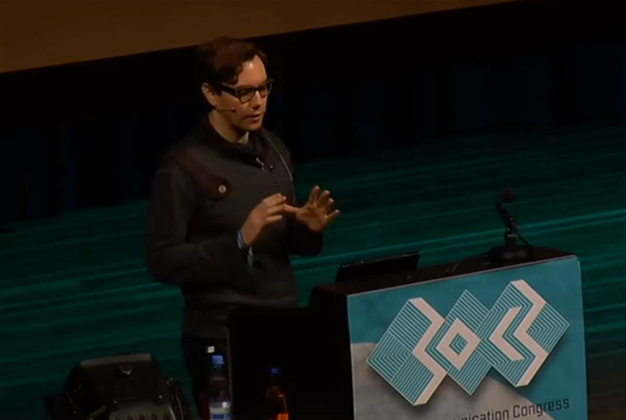
Delivering a keynote speech at the 30th Chaos Computer Club conference in Hamburg, Germany, Tor contributor-cum-Der Spiegel journalist Jacob Applebaum presented a snapshot of dozens of zero day exploits used to spy on both US citizens and foreigners.
Applebaum revealed numerous leaked NSA-branded slides detailing the agency's armoury of exploits - most of which are yet to be published by any news outlet, providing fleeting glimpses of the headlines SC readers should expect to see over the coming weeks.
[See slidedeck: The NSA's spyware catalogue].
Applebaum, a cryptography expert, was yesterday named as an author of an explosive article in Der Spiegel listing the names and details of several NSA exploits. The Germany magazine published NSA documents that boasted of the agency's ability to use zero-day exploits to spy on communications passing through the switches and routers of the world’s largest networking vendors, Cisco, Juniper Networks and Huawei, among others.
Today, he detailed previously unreported exploits targeting the most popular lines of servers manufactured by Dell and HP, as well as smartphones of Apple and Samsung.
Applebaum made no apologies for naming the companies in his presentation.
“F### them for collaborating, and for leaving us vulnerable,” he said.
By naming the companies, he added, the pressure builds for these technology vendors to come forward and disclose whether they were co-conspirators in the NSA’s spying efforts, or fellow victims.
“In order to have truth and reconciliation, we need a little truth,” he said.
HIDDEN IN THE BIOS
Applebaum explained that the NSA had compromised many of these server hardware systems at the BIOS level.
The BIOS (basic input output system) is firmware that provides the most basic instructions to a system on how to operate the hardware. This has perplexed security researchers, he said, as they “don’t have the forensics tools” to locate the malware, even when they can see its result.
The NSA’s documents boast that these exploits work across servers running the Microsoft Windows, Linux, FreeBSD and even Sun Solaris operating systems.
“How many people in Al Qaida are using Solaris?” Applebaum asked the crowd, referring to an operating system now owned by Oracle and most often used by western telcos, large banks and other corporations.
“[The NSA] are interested in compromising systems, not just people," he said. "They want to colonise systems with these tools.”
One NSA-created slide specifically pointed out that Dell’s best-selling PowerEdge servers (1850, 2850, 1950, 2950), which the Texas-based vendor has sold in Australia since 2005, all feature a vulnerability that allows the NSA to post spyware iton the BIOS using either remote access or via the inserting of a USB drive.
[The humble USB drive, often handed out as free gifts at IT fairs, was the expected attack vector for the Stuxnet virus, which sabotaged an Iranian power plant and several other industrial systems across the globe that used the same Siemens controller as Iran's nuclear enrichment program.]
A related NSA exploit - named GODSURGE - uses a JTAG debugging interface in the Dell PowerEdge 1950 and 2950. A JTAG debugging interface is usually used to test the BIOS/firmware for bugs, but it can also be used to reflashthe BIOS from scratch.
“Why did they release these servers with that software?” Applebaum asked the audience. “Is that a bug or a backdoor? This is an Advanced Persistent Threat.”
HP’s popular Proliant 380DL G5 server was named in an NSA slide as being a target for another tool, IRONCHEF, which extracted data from the server using two-way RF communication.
This exploit, however, required what the NSA terms ‘interdiction’ - physical access to a target’s server for the installation of a hardware-based implant. Physical access usually requires an NSA operative to break-in to a premises, to detain a suspect and confiscate their computers and smartphones, or - as Der Spiegel sensationally reported yesterday - for NSA agents to intercept newly purchased computing devices before they are shipped to a target.
PERSONAL DEVICES
Beyond servers and switches, the NSA’s extensive list of exploits included IRATEMONKEY, which replaces the firmware on hard drives produced by Western Digital, Seagate, Maxtor and Samsung to retrieve data from laptops and desktop computers.
One NSA slide revealed how a combination of the SOMBERKNAVE, VALIDATOR and OLYMPUS exploits can be used to extract data from Windows XP PCs that are “air-gapped”, i.e. not connected to any public networks. After taking control of a nearby wireless access point, SOMBERKNAVE is able to connect to a machine even if its embedded 802.11 device (WiFi cards are standard fare in business and consumer PCs) has been disabled.
A further slide revealed that the NSA has developed USB cables called COTTONMOUTH that - whilst appearing to be industry standard - feature embedded bugs to tap wireless network traffic and gain access to a user’s machine.
Once a target is mobile and connecting to cellular or WiFi networks, the NSA has further tools up its sleeve.
The NSA has developed its own base station routers as well as tools that mimic base stations - the latter being a ‘GSM Telephone Tripwire’ imaginatively named ‘CANDYWIRE’.
Applebaum also briefly touched on MONKEYCALENDAR, a software implant the NSA has developed for injection into the SIM cards of GSM (mobile) phones. This software, injected either over the network or physically via a USB smart card reader, keeps the NSA continually abreast of its location by sending geolocation data to the NSA via encrypted SMS. The NSA slide suggests this exploit may require the cooperation of the target’s mobile network provider.
The NSA has also developed exploits for tapping Apple’s iPhone (DROPOUTJEEP) and Microsoft’s Windows Phone (TOTEGHOSTLY), revealing the device’s location, reading its SMS, voicemail and contact list and providing remote control of its camera and/or microphone, but at the time the NSA slides were leaked, the agency still required physical access to the phones to install its software bugs. That said, the NSA’s ANT team claimed to be pursuing a remote installation capability.
THE SEARCH FOR MALWARE
Applebaum told the 30c3 audience that he expects the InfoSec community to now search systems for evidence of the NSA malware in use.
“A lot of malware researchers will have a lot to say about this in the future,” he said.
Indeed, Applebaum referred to the work of Kartsen Nohl, a German security researcher who in 2010 boasted at the same conference that SIM card encryption could be hacked, and returned in July 2013 at the Black Hat conference to prove beyond doubt that SIM cards could be compromised.
“The NSA says that nobody will come to harm” from its computerised spying programs, Applebaum said, as the hacking tools it has created “will never be used by a third party”.
The fact that Nohl’s team at Security Research Labs used some of the same techniques as the NSA to gain access to SIM cards proved “how wrong the NSA is on this," he said.
The danger for users, Applebaum reasoned, was that “for every Karsten there are hundreds of people paid to do this full-time who never tell anybody”, referring to criminal hackers that break into networks for financial gain.
He also left IT security managers with a handy tip to begin their search. He suggested they search for suspect traffic sent via the UDP protocol and secured by the RC6 encryption algorithm developed and freely released by RSA Technologies, which prior leaks suggest was the recipient of a $10 million prize for its efforts to aid the NSA.
“If you work for the NSA, I’d like to encourage you to leak more documents,” Applebaum concluded.
“I’ll be available until I am assassinated to answer questions.”










.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



