Cyberoam has denied allegations by the Tor Project that its Deep Packet Inspection (DPI) boxes were “mass surveillance devices” capable of intercepting a wide range of traffic.

The security vendor was embroiled in controversy last week after Tor security researcher Runa Sandvik and OpenDNS’ Ben Laurie concluded its DPI units had intercepted traffic from a user from Jordan.
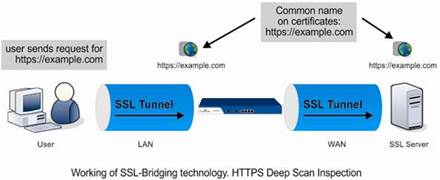
They discovered that the Unified Threat Management (UTM) units used shared certificates which users must accept to have their encrypted traffic scanned, ostensibly for security threats.
Users accepting the certificates could be scanned by any Cyberoam DPI unit, researchers said. Moreover, they claimed the private key could be extracted from the devices.
But Cyberoam fired back, stating its keys could not be extracted.
“.. theoretically it is possible to decrypt SSL data using a conned private key. Cyberoam UTM does not allow import or export of the foresaid private key used for the SSL-Bridging technology,” the company said on its blog.
“Cyberoam UTM either accepts or rejects, but does not store HTTPS Deep Scan Inspection data, as processing is done in real-time. The possibility of data interception between any two Cyberoam appliances is hence nullified.
“Having vindicated Cyberoam technology, we appreciate Tor for the awareness campaign.”




.jpg&h=140&w=231&c=1&s=0)





 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



