A joint operation by security vendors, content delivery networks and Google has resulted in the abolition of the large-scale WireX Android botnet.
Researchers from Akamai, Cloudflare and Oracle's Dyn worked with their counterparts at security vendors Flashpoint, RiskIQ and Team Cymru on the anti-botnet operation, after discovering denial of service attacks emanating from Android devices compromised by WireX.
WireX appeared earlier this month, performing minor volumetric denial of service attacks that went unnoticed at the time.
Towards the middle of the month however, WireX attacks from over 70,000 IP addresses were discovered, hitting both content delivery networks and providers. In some attacks, over 160,000 IP addresses were involved, Akamai said.
The attacks were HTTP GET requests, and arrived from more than 100 countries, an unusual trait for DDoS botnets, the researchers said.
WireX can also encrypt the data it sends with transport layer security (TLS), making it difficult to separate out attack traffic.
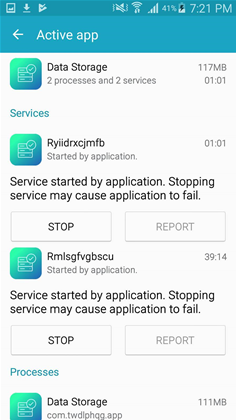
Google was alerted to the existence of WireX by the vendors and removed over 300 infected Play Store apps that hid the malicious features from users.
Its PlayProtect anti-malware feature now prevents apps that contain WireX from being installed. Google is also removing the malware from devices.
It is not yet known who is behind the attacks, which mostly hospitality industry sites.
Analysis of the malware suggests WireX started life as a click-fraud bot targeting advertising companies to generate fake impressions.
The tech companies were inspired to collaborate on the effort after seeing the response to the large-scale Mirai botnet attacks earlier this year.
Mirai crippled companies such as Oracle Dyn, and saw content delivery networks capture and analyse DDoS traffic to help security vendors identity the malware activity.
The researchers believe such collaboration between competing companies will help the industry handle internet-wide security problems.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



