A piece of malware used by Western governments is most likely coded by the same developers behind the Regin malware that has been used to spy on telecommunications operators around the world.
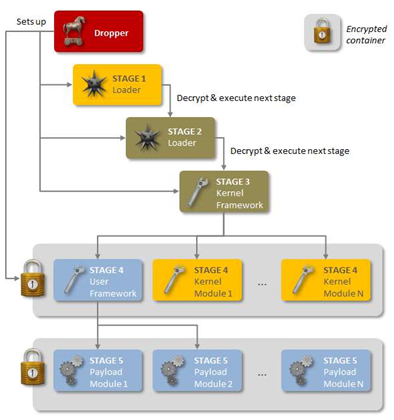
Security vendor Kaspersky compared the 20123.sys kernel-mode driver for the QWERTY keylogger - part of the WARRIORPRIDE malware framework discovered earlier this year - and found it had been built from the same source that created the 50251 plugin featured in Regin.
WARRIORPRIDE first came to light earlier this year after German magazine Der Spiegel published documents leaked by former United States National Security Agency contractor Edward Snowden revealing the existence of the malware and its use by Western government.
The publication also released an archive of the QWERTY keylogger plug-in for WARRIORPRIDE [PDF] to allow it to be analysed by independent experts, such as Kaspersky.
The company's researchers have now concluded that the two APT malwares were created by the same organisation.
"Considering the extreme complexity of the Regin platform and little chance that it can be duplicated by somebody without having access to its source codes, we conclude the QWERTY malware developers and the Regin developers are the same or working together," the researchers wrote.
The infosec industry has long been aware of Regin but information on the malware only began being published en masse late last year after security firm Symantec released a white paper on Regin, prompting others to go public with their knowledge.
Regin has been used against telecommunications companies, businesses and individuals worldwide, and aims to steal login credentials and sensitive data. The malware was discovered to have been behind an attack on Belgian telecommunications company Belgacom.
Security experts believe the malware is developed by American and British security services.
The US Computer Emergency Readiness Team (US-CERT) issued an alert last November warning users about Regin, calling it "a sophisticated backdoor Trojan used to conduct intelligence-gathering campaigns".
Regin has been found in 14 different countries around the world, but not in the Five-Eyes alliance nations United States, Canada, Australia, United Kingdom and New Zealand.





.jpg&h=140&w=231&c=1&s=0)

_(39).jpg&w=100&c=1&s=0)



 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



