Researchers have discovered a new worm that utilises exploits leaked from the US National Security Agency (NSA), following the destructive WannaCry ransomware outbreak.
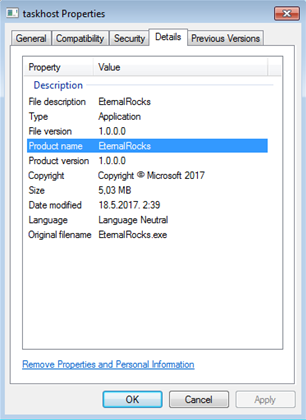
Dubbed EternalRocks, like WannaCry the worm targets vulnerable implementations of Microsoft's Server Message Block (SMB) file sharing protocol.
Penetration tester Miroslav Stampar, also a member of the Croatian government computer emergency response team, captured a sample of the worm and posted an analysis on Github.
EternalRocks is also known as MicroBotMassiveNet and BlueDoom. It utilises seven SMB exploits: ETERNALBLUE, ETERNALCHAMPION, ETERNALROMANCE and ETERNALSYNERGY, along with DOUBLEPULSAR, ARCHITOUCH and SMBTOUCH.
EternalRocks uses a two-stage attack on target systems, starting with infecting unpatched Windows systems and downloading further malware components and a TOR browser for obfuscated communications with a command and control server.
The second stage of the attack sees EternalRocks activate after 24 hours, with the above SMB exploits downloaded and the worm scanning the internet for systems that listen on TCP port 445.
EternalRocks has no current payload like the ransomware encryption module of WannaCry, and only spreads itself among vulnerable systems.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards












_(1).jpg&h=140&w=231&c=1&s=0)



