The Necurs botnet appears to have dropped the infamous Locky ransomware in favour of an aggressive spam campaign pushing dubious financial information.
Researchers have noticed a drop in the volume of Locky campaigns while observing the emergence of a new spam campaign.
Necurs is a massive botnet which was once the prime driver for the Dridex banking Trojan, and Locky ransomware.
However it seems to have moved away from Locky since the end of last year, when Cisco's Talos team observed a noticeable drop in the botnet's use of the ransomware.
Locky campaigns are still being deployed, but at volumes far diminished from the hundreds of thousands of messages that a Locky campaign sent in its heyday.
Ondrej Kubovič, security specialist at ESET, said Locky had been in decline from an even earlier date than first thought, claiming to have spotted a decline since last August.
But he declined to comment on the cause of the drop.
"It would be merely our speculation as only ransomware operators know their own motivations.”
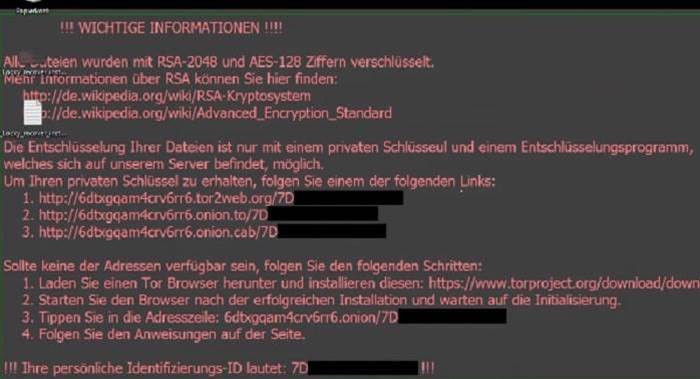
Locky has been a very popular brand of ransomware since its birth in February 2016, and was regularly updated with new techniques.
Like most malware, it has been traditionally delivered via email and activated when its unlucky victims opt to enable the macros on an attached document. Once that trap is sprung, Locky sets about encrypting the files on the targeted computer.
Locky has been seen in a variety of high profile attacks including the 2016 breach on the Hollywood Presbyterian Medical Centre, in which the hospital had to pay US$17,000 to retrieve its data.
The ransomware has been historically tied to Necurs; in June 2016, when the botnet went offline, Locky campaigns dropped in kind.
Losing favour
But now Necurs appears to have changed course in favour of more sophisticated scams. Security researchers have noticed the botnet sending out barrages of spam giving out dubious financial information.
Recently noticed spam sent through the botnet touts a company called inCapta as set to rise in value. The emails encourage the recipients to buy inCapta stock, which they claim will skyrocket tenfold in the next few days due to a new piece of groundbreaking drone technology.
inCapta, according to the message, is due to acquired by a company called DJI (“the most prominent drone-maker in the world”).
The email proclaims “this has the potential to literally change the world of news broadcasting as we know it”.
It promises “a premium of over 1000 percent over Friday's closing price. Tell all your friends about INCT (inCapta) and make sure you buy it as soon as possible today at any price under 20 cents a share to guarantee yourself massive profits".
Security researchers dubbed the campaign a pump and dump scam.
A pump and dump fraud is a scam in which stock is artificially inflated before before being sold en masse, ensuring that those operating the scam reap the rewards of the inflation while leaving their victims in the lurch.
Necurs seems to be pursuing this new business aggressively.
Conrad Longmore, a security researcher who has published examples of the email on his blog, said it had been "a long time since I've seen a pump and dump spam run illegally pushing a stock as hard as this".
InCapta did not respond to several requests for comment.










 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



