After first dismissing a security researcher's findings of flaws in the built-in Remote Desktop Protocol (RDP) client in Windows, Microsoft has now issued a patch for the vulnerability after being told it could be used to break out of the Hyper-V hypervisor.
Named Poisoned RDP vulnerability (CVE-2019-0887), the flaw and others in the mstsc.exe client were first documented by Check Point researcher Eyal Itkin in February this year.
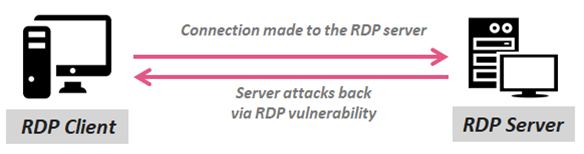
Itkin discovered a path traversal bug in the shared clipboard code that lets attackers lay in wait on compromised machines, waiting for users to connect.
As the shared clipboard allows users to copy files from one computer to another, it was possible to abuse the RDP client not properly sanitising the paths received, allowing attackers to plant malicious code on remote systems.
Clients and servers also communicate with each other, sending messages notifying when the clipboard is updated. Malicious servers can tell when clients copy data to the clipboard and read it, Microsoft said.
Fake clipboard updates without actual copy operations can also be done by malicious servers. This allows them to control the client clipboard without users noticing, the company added.
As the attacker's behaviour would not stand out as unusual, RDP anomaly detection wouldn't be useful to warn about an attempt to compromise clients.
In February, Microsoft acknowledged the problem but didn't think it was worth patching as it didn't meet the company's. bar for servicing.
However, Microsoft has now done a full one-eighty after being told by Itkin that the bug allows guest to host sandbox escapes on its Hyper-V hypervisor, used for virtualisation including in its Azure cloud.
Itkin noted that Hyper-V uses RDP for managing virtual machines, and inherits the vulnerabilties in the remote management protocol.
Microsoft has now added detection logic to its Defender Advanced Threat Protection to spot the RDP attacks Itkin described and released a patch last month for Windows.
The company said it had been taught "several lessons in security", including learning how the clipboard feature originally designed for local use works in new environments.





.jpg&h=140&w=231&c=1&s=0)





 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



