A type of ransomware targeting Android users visiting pornographic sites is making the rounds in Australia, with thousands of people being subject to extortion attempts with messages purporting to be from local law enforcement.

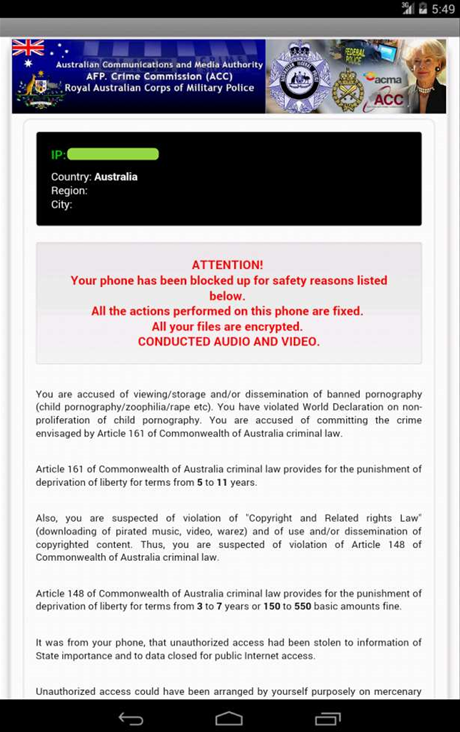
Named Koler, the malware reported by Kaspersky security researchers locks the screen with a popup and displays custom messages for thirty countries claiming to be from law enforcement, while demanding a ransom of US$100 or US$300 to unlock the display.
The message for Australia makes mention of several authorities, including the Royal Australian Corps of Military Police and the Australian Communications and Media Authority (ACMA).
Victims are accused of having accessed illegal pornography and copyright infringement, and threatened with prison sentences and fines.
Kaspersky said that despite the ominous message displayed, Koler does not encrypt users' data, or lock people out of their devices.
According to Kaspersky telemetry data, the ransomware has struck 6,223 Australian visitors to the mobile domain spreading the infection, the third highest in the world after the United States and the United Kingdom.
In total, over 200,000 Android devices around the world were infected with Koler.
Koler is spread through visits to malicious pornographic sites that are part of a large malware distribution network.
Kaspersky said the use of porn sites is intentional, to make victims feel guilty and thus be more likely to pay the ransom.
Users are asked to download and install a malicious application on their Android device but the malware campaign can also redirect to sites containing the Angler exploit kit that can attack PCs running Microsoft's Internet Explorer web browser.
Koler is thought to have been active since May this year, with security researcher Kaffeine credited with first discovering the malware.
The malware appears to be from Russia, developed by the Reveton ransomware authors that use similar fake threats from law enforcement.
According to Kaspersky, the Koler malware campaign is currently winding down, with the command and control centre sending out uninstall commands.
The security firm said it is working with the Europol and Interpol trans-national police organisations to close down the ransomware distribution infrastructure.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



