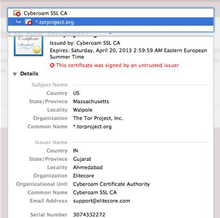
Enterprises using Cyberoam deep packet inspection devices could have traffic intercepted by anyone using its shared certificate.
Tor Project security researcher Runa Sandvik and OpenSSL's Ben Laurie discovered the devices used the same Certificate Authority certificate and private key.
That gaffe made it possible for any DPI box to grab traffic from employees monitored by Cyberoam devices.
“It is therefore possible to intercept traffic from any victim (employee) of a Cyberoam device with any other Cyberoam device — or, indeed, to extract the key from the device and import it into other DPI devices, and use those for interception,” Sandvik said in an advisory.
“Victims should uninstall the Cyberoam CA certificate from their browsers and decline to complete any connection which gives a certificate warning.”
Sandvik and Laurie began researching the hole after a Tor user in Jordan reported seeing a fake Cyberoam certificate for the TorProject.org. They discovered the user’s traffic was intercepted by a Cyberoam device.
Trusted certificates had to be installed on employee machines, referred to as victims, in order for DPI to work. But that Cyberoam victims all installed the same trusted CA which would issue fake certificates was “a little surprising” Sandvik said.
The Tor boffin alerted Indian-based Cyberoam about the flaw (CVE-2012-3372) on June 30 and her intention to publish an advisory on July 3.
The company acknowledged the vulnerability and said it would investigate. The company has been contacted by SC for comment.
Users can delete the root CA by following these instructions.



.jpg&h=140&w=231&c=1&s=0)






 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



