The fourth version of the CryptoWall ransomware has landed in the wild, equipped with better evasion techniques and tactics to thwart antivirus protection and detection.
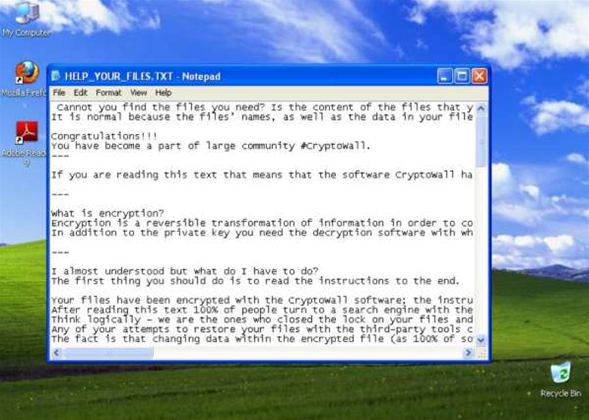
Ransomware attacks computers and encrypts user files and folders via infected email attachments, with attackers demanding ransom payments to unlock the scrambled documents.
Users are told to make the payment by a specific deadline or risk having the private key to unlock the files deleted.
The active CryptoWall ransomware spawned from CryptoLocker, which is thought to have extorted more than $3 million from victims before the botnet used to distribute it - Gameover Zeus - was taken down last year.
The CryptoWall variant began spreading in Australia late last year. It operates in the same manner as CryptoLocker but uses emails purportedly sent from Australia government organisations such as the tax office and Australia Post.
A third variant of the ransomware landed early this year, and researchers have now discovered a fourth version in the wild.
Heimdal Security called CryptoWall 4.0 a "new, powerful ransomware strain".
"The truth is that it’s even more challenging to protect victims against CryptoWall 4.0 than from its predecessor," they wrote in a post.
Cryptowall 4.0 has "vastly improved communication capabilities" as well as a "modified protocol that enables it to avoid being detected, even by second generation enterprise firewall solutions".
"This lowers detection rates significantly compared to the already successful Cryptowall 3.0 attacks," the researchers wrote.
The ransomware also now alters file names as well as file contents to make detecting what has been encrypted more difficult, the firm said.
"This social engineering technique confuses the victims even more. It also enhances the pressure of wanting to retrieve their data as fast as possible," the Heimdal researchers wrote.
"Consequently, this increases the “success” ratio of how many victims see the message versus how many pay the ransom. A clear business enhancement by cyber criminals."
CryptoWall 4.0 still uses The Onion Router (TOR) network - which hides senders and recipients - to direct victims to payment instructions, and also still connects to a number of compromised web pages to download the payload onto the victim PC.
The ransomware is still able to evade most antivirus, and continues to spread via drive-by attack and spam mail.
To avoid getting caught by CryptoWall, the security firm recommended keeping systems up to date, constantly backing up data, avoiding emails with attachments sent by unknown senders, and using products that can detect and block recent ransomware variants.




.jpg&h=140&w=231&c=1&s=0)






 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026











_(1).jpg&h=140&w=231&c=1&s=0)



