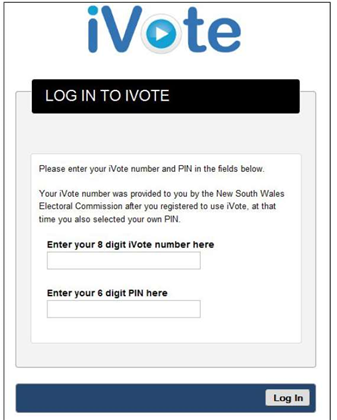
NSW's online voting system iVote has been discovered to contain a critical flaw just days before the state's citizens head to the polls for the 2015 election.
Two university researchers over the weekend revealed that the system's voting server had loaded code from a third-party website vulnerable to the recently discovered FREAK attack.
The FREAK flaw in the Secure Sockets Layer/Transport Layer Security (SSL/TLS) cryptographic protocols allows attackers to intercept HTTPS connections between vulnerable clients and servers.
Users of web browsers on Android and Apple smartphones were left vulnerable to the attack.
The two researchers - Vanessa Teague from the department of computing and information systems at Melbourne Uni, and J. Alex Halderman from the University of Michigan's computer science faculty - found that the flaw in iVote allowed attackers to intercept a NSW voter's web traffic.
The iVote website included additional JavaScript from an external server - ivote.piwikpro.com - which is vulnerable to a range of SSL attacks, including FREAK.
An attacker could exploit FREAK to manipulate a voter's connection to the external Piwik (analytics firm) server and inject different code into iVote, the researchers wrote, allowing them to change and read votes.
Technology companies have been rushing since the FREAK flaw was discovered to patch affected browsers, but a number still remain vulnerable.
"We demonstrated that we could make the voter’s web browser display what the voter wanted, but secretly send a different vote to the iVote voting server," the researchers wrote.
While iVote offers a vote verification process - which involves calling an automated phone line to confirm their vote - the researchers said they had no way of checking whether that system was secure.
"[It] could have errors or security vulnerabilities; we can’t tell you with any certainty either way, since there’s no publicly available source code or system details," the pair wrote.
Teague and Halderman tested the vulnerability on a practice vote through the iVote practice server, and later verified that the same flaw affected the real voting server before alerting the CERT Australia on Friday.
The NSW Electoral Commission updated iVote to disable the code from piwikpro.com on Saturday, the researchers said.
NSW citizens have been able to cast votes through the iVote system since March 16 ahead of this Saturday's state election. The platform is open to those who live more than 20km from a polling booth, blind and disabled citizens, and those interstate or overseas on election day.
The NSW Electoral Commission has forecast more than 100,000 voters will use iVote for the 2015 election, compared to the 46,800 - equivalent to 1 percent of total votes - who used it in 2011.
The state government last year awarded Spanish firm Scytl a five-year, $1.9 million contract to expand iVote for the 2015 state election.
iVote was first used in 2011 in a limited capacity. It is an online application built on JavaScript and HTML.
Around 66,000 people have already registered their vote through iVote for the 2015 state election.
Teague and Halderman recommended those who are yet to vote avoid using the online platform.
"We hope there are no more exploitable security problems in iVote and that the rest of the NSW election runs more smoothly," they wrote.
"But since we’ve had no opportunity to inspect the server side code or systems, there’s no way to be sure. When you’re working on the internet, new vulnerabilities emerge all the time."
The NSW Electoral Commission said the research did not provide any evidence of an actual breach of the iVote production system.
"We have sought advice from the iVote core system service provider and our internet security consultants CSC Cybersecurity Australia," a spokesperson said in a statement.
NSWEC IT director Ian Brightwell told iTnews the overal risk of a man-in-the-middle attack being successfully implemented was considered low.
"The third party analytics tool identified as vulnerable used a private instance of Piwik analytics and held anonymised data," Brightwell said.
"The decision to use this service was considered at the time of implementation to have acceptable risk level.
"However, given the recent media releases it was decided that the connection to this server should be terminated to ensure public could retain confidence in the iVote system."



.jpg&h=140&w=231&c=1&s=0)
.jpg&h=140&w=231&c=1&s=0)






 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 Forrester's AI Forum Sydney
Forrester's AI Forum Sydney
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



