Coding errors in the WannaCry ransomware worm that ripped through hundreds of thousands of Windows computers mean users can restore files without having to pay the ransom, security experts have found.
"From our in depth research into this ransomware, it is clear that the ransomware developers have made a lot of mistakes and, as we pointed out, the code quality is very low," Kaspersky researchers said.
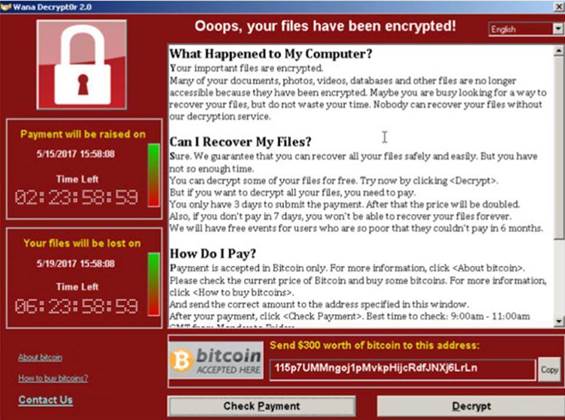
When activated, WannaCry reads files on victim machines and makes encrypted copies before attempting to delete the original, unscrambled data.
However, the programming logic in WannaCry is faulty and the file deletion can fail, or is performed in a way where the user data isn't overwritten and can be restored.
Files on drives that do not contain the Windows operating system can be restored with data recovery tools because WannaCry fails to remove them properly, the Kaspersky researchers noted.
On a Windows system drive, WannaCry will overwrite files stored in the Desktop, Documents and other important user folders. If this happens, there is no way to restore the data, the researchers said.
However, files not stored in important user folders like Documents are moved to a temporary directory. In this case, Kaspersky observed that the files are not overwritten, and can be restored with data recovery software.
WannaCry also falls over when it encounters files that are marked as read-only and cannot be written to.
The malware creates an encrypted copy of such files and leaves the original in place with the "hidden" attribute set.
Again, this makes restoration of the files easy, by simply unsetting the "hidden" attribute, Kaspersky said.




_(37).jpg&h=140&w=231&c=1&s=0)
_(33).jpg&h=140&w=231&c=1&s=0)

_(39).jpg&w=100&c=1&s=0)



 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



