Apple has released an unexpected, large security update for its macOS, iOS, iPadOS and other device operating systems, that handle no fewer than seven critical security issues.
Critical flaws allowing arbitrary code execution through memory corruption were patched in the AppleScript scripting language, the Accelerate Framework, and the ImageO and AppleAVD picture handlers.
The Safari Webkit rendering engine was patched against a flaw that allowed attackers to run malicious code through crafted web content, due to a use-after-free memory management issue.
Two flaws in the macOS Login Window for user authentication were also patched.
One allowed attackers to view previously logged in users' desktops from the Fast User Switching screen.
A more serious bug let attackers to bypass the Login Window completely, provided they had access to the target Mac.
At least one of the bugs took Apple a long time to sort out.
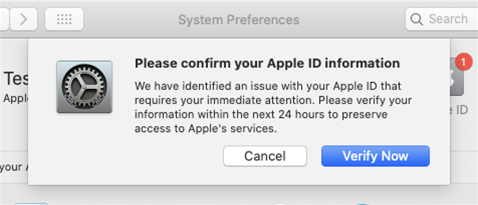
A Brazilian resarcher, Guilherme Rambo, wrote that in December 2020, he reported a vulnerability in the macOS and iOS CoreFollowUp component that could be used to create very convicing phishing attacks.
The CoreFollowUp allowed attackers to display malicious "Verify your Apple ID" and "Finish Setting Up Your Device" dialogs, as arbitrary processes were allowed to send commands to the followupd daemon, tricking users into thinking the on-screen system messages are legitimate and capturing their account login credentials.
A partial fix appeared in macOS 11.3 released end of April 2021, which came with a link of permitted URLs for the system dialogs.
In August 2021, Rambo received a US$5,000 bug bounty award from Apple but only today did a complete fix arrive, that prevents arbitrary system processes from communicating with the followupd to register notifications, for macOS 12.3.
Rambo noted that third-party apps on macOS ship with their own privileged daemons that accept connections from processes without authentication, and which could be abused for malicious purposes.


.jpg&h=140&w=231&c=1&s=0)




_(39).jpg&w=100&c=1&s=0)



 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



