The biggest distributed denial of service attack in history was caused by magnification and reflective amplification, likely by using a botnet.
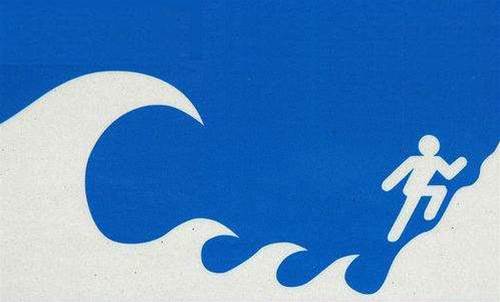
The 300Gbps DDoS attacks sent by an alleged spamming outfit against spam fighters SpamHous dwarfed some of the biggest 100 or 200Gbps attacks.
It used DNS reflective amplification, according to Arbor Networks solutions architect team manager Darren Anstee, in which attackers used internet infrastructure to magnify the size of the attack.
“When you visit a website you send a domain name server (DNS) query to the DNS server and this responds with the answer that resolves the domain name to the IP address, and the responses can be large," Anstee said.
“Here, the attacker is creating small DNS query packets and open DNS resolvers are responding with large responses.
The attackers have spoofed the source IP address used in the initial queries to be the intended target of the attack, and thus the DNS resolvers respond to the victim (Spamhaus) with the much larger response packets – magnifying the attack capability of the attacker.”
Responses to DNS queries can be many times larger than the original query, especially if an ANY query type is used, Anstee said.
"As DNS is a UDP protocol, the receiving DNS resolver simply trusts that the originator of the query has used their own valid IP address as the source of the request, and responds accordingly. DNS reflective amplification attacks, as these are known, leverage the fact that some operators do not filter traffic from their users – to ensure they are using the correct IP ranges – and the fact there are many open DNS resolvers out there which will respond to a query from anyone."










 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



