Industrial control experts have lashed out at industrial control systems vendor Siemens for failing to patch serious vulnerabilities identified in its Programmable Logic Controllers (PLC).
The S7-300 and S7-400 controllers are core components of Siemens' Supervisory data Acquisition and Control (SCADA) systems, which the company claims to be in use "in a wide variety of industrial applications worldwide".
Researcher Dillon Beresford revealed at Black Hat that he found a hardcoded username and password in the firmware of the controllers, plus a series of security compromises that he said Siemens had failed to fix despite knowing of the flaw for more than a year.
The login details accessed a telnet and http server which were superfluous to the PLC.
Dillon said he was able to log in and then "dump memory, delete files and execute commands”.
The news riled SCADA security experts.
Eric Byres said he was "embarassed" to have earlier praised the company for its incidence response and quality assurance.
"Letting unnecessary services run on a PLC and the use of hardcoded passwords are both basic security errors. This should have never been allowed through the Siemens development and quality assurance process.
"Even knowing that the bad news was going to come out, they have done little. Their current advisory provides no useful guidance. There are simple mitigations such as placing a firewall in front of the PLCs to block the http and telnet. Setting up a basic IDS to check for the string “Basisk” would also be a simple solution.
"None are proposed by Siemens."
DigitalBond SCADA consultant Dale Peterson said the vulnerabilities were likely the tip of the iceberg.
"My view is Siemens has a complete lack of an SDL based on the other vulnerabilities Dillon and others have identified," Peterson said. "Control of the engineers is not even close to the biggest problem."
SCADA expert and analyst of the Stuxnet malware Ralph Langer agreed with the assessment.
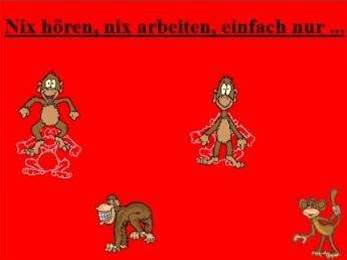
Dillon also found a "dancing monkeys HTML Easter egg" graphic coded into the firmware by Siemens developers. That move led some to question Siemens quality control.




.jpg&h=140&w=231&c=1&s=0)





 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



