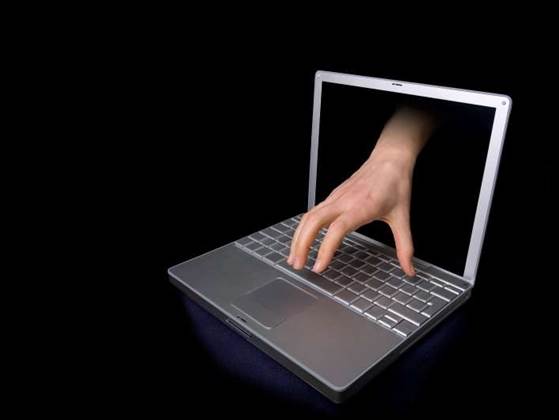
According to the Sunbelt malware research team, the screensaver spam is pointing to a site put up by Loads.cc website, indicating that the gang, said to be responsible for distribution and installation of numerous spambots, keyloggers, DDoS bots, adware and rootkits, is back in business.
The group behind Loads.cc, believed to be based in Russia, shut down their original domain address in January after suffering suffered a DDoS attack from a rival malware gang utilising a Barracuda botnet, the Sunbelt team said.
After one of the infected screensavers is installed by the recipient, malware activates an HTTP GET request for a PHP script (manda.php), which may return a URL of additional malware for the bot to retrieve and install.
See original article on scmagazineus.com










 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



