RSA has offered to replace all SecurID authentication tokens in an effort to regain its customers' trust, according to the EMC security division’s boss Art Coviello.
The decision to replace tokens was spurred on by recent attacks on defence contractor Lockheed Martin, which exploited information stolen during a breach RSA disclosed in mid-March.
“We recognise that the increasing frequency and sophistication of cyber attacks generally, and the recent announcements by Lockheed Martin, may reduce some customers' overall risk tolerance,” said Coviello in an open letter published Tuesday.
The attacks on Lockheed Martin and rumoured attacks on Northrop Grumman bring into question Coviello’s earlier claim that the breach against it would “not enable a successful direct attack” on its SecurID customers.
The company may need to replace as many as 40 million tokens, used across the many of the world’s largest organisations in government and industry, according to Ars Technica.
Australian customers that may take up the replacement offer include Telstra's directories business Sensis, insurer Allianz Australia and Virgin Blue.
For business customers that use tokens to authenticate customer transactions, RSA has offered to implement “risk-based authentication strategies”.
Coviello remained confident that customers that implemented the remediation steps RSA had offered would keep them protected.
RSA knew the likely targets of the attack on it were defense contractors, which was why it had already embarked “on an accelerated timetable” for those customers, he said.
“The perpetrator's most likely motive was to obtain an element of security information that could be used to target defense secrets and related IP, rather than financial gain or public embarrassment,” said Coviello.
Coviello suggested in an interview with the Wall Street Journal that the replacement offer was partly driven by recent attacks Sony, Epsilon, Google, PBS and Nintendo. Although these had nothing to do with the attack on Lockheed Martin, they had changed customers' appetite for risk.
"Because of these attacks and the changing threat landscape there has been and incredible heightening of public awareness," said Coviello.
"The whole thing has reached a crescendo where customers don't want to tolerate any level of risk, whether it's real or perceived."
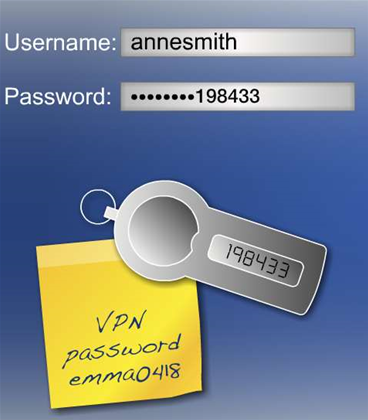
RSA disclosed in April that the “advanced persistent threat” that exposed its information was a booby-trapped email to its human resources staff. The attackers had used a Flash exploit to gain initial entry and later worked their way up the company’s ranks.



.jpg&h=140&w=231&c=1&s=0)







 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



