Security researchers have seen a sharp uptick in hackers attempting to exploit popular online communications platforms in order to compromise users' systems using malware.
Every leading communications platform has been targeted by cyber criminals setting up phishing websites, including the Zoom video conferencing and Microsoft Teams collaboration suites, security vendor Check Point warned.
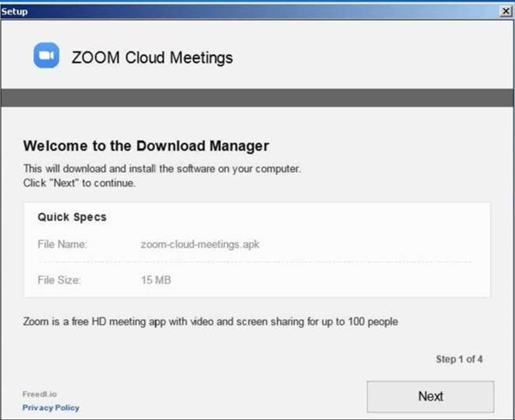
Check Point had found malicious files with names crafted to make them appear as bone fide Zoom and Microsoft Teams applications, but which install the InstallCore program.
InstallCore is classified by security vendors as a potentially unwanted application (PUA) threat, which can be used to install adware and malicious applications.
More than 1700 new domains with the name "zoom" in them have been registered since the beginning of the year, and a quarter of them in the last week, Check Point said.
Four per cent of the newly registered domains have malicious characteristics, the security vendor said.
Google's official classroom.google.com web based educational tool has also been targeted with phishers registering deceptive domains like googieclassrom.com.
Users of remote working and learning tools are advised to take extra care if they receive emails and files from unknown senders, particularly if they contain special deals or discount offers.
Clicking on links and opening unknown attachments in the emails is dangerous and could lead to computers being taken over, and users are advised not to do that.
Check Point also advised users to look for lookalike domain names that try to impersonate legitimate ones, spelling errors in emails and websites and be cautious of unfamiliar email senders.




_(37).jpg&h=140&w=231&c=1&s=0)


_(39).jpg&w=100&c=1&s=0)



 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



