Users of Linux distributions that operate the systemd initialisation framework are advised to patch the networkd-dispatcher connection status change daemon, after Microsoft security researchers discovered two root privilege elevation bugs they named Nimbuspwn.
Several security concerns were found in the code for networkd-dispatcher shipping with Linux desktop systems.
These include directory traversal, and race conditions in symlink and time-of-check-time-of-use (TOCTOU), that could be abused by attackers to obtain root privilege escalation.
"We discovered the vulnerabilities by listening to messages on the System Bus while performing code reviews and dynamic analysis on services that run as root, noticing an odd pattern in a systemd unit called networkd-dispatcher," Microsoft's 365 Defender Research Team wrote.
The messages were transmitted on the Desktop-Bus or D-Bus, an inter-process communications (IPC) channel software bus developed by the FreeDesktop graphical user interface project.
D-Bus exposes a global System Bus, which has listening services running as root, making it attractive for attackers.
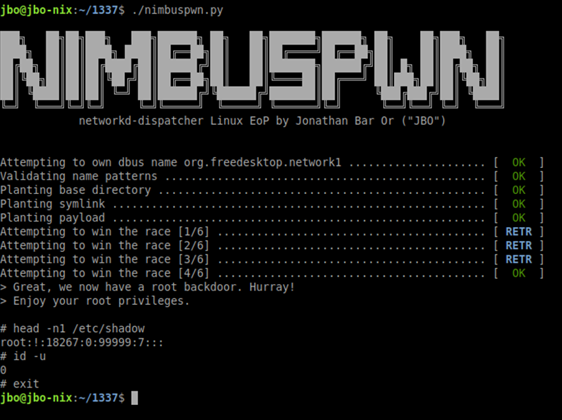
Chained together, exploitation of the Nimbuspwn vulnerabilities is a multi-step process that allows attackers to run their own files as the root super-user, with full access to all parts of the Linux system.
The researchers were able to activate a root backdoor on a vulnerable system, as a proof of concept.
Apart from deploying root-privilege backdoors and performing malicious actions as a super-user, the Nimbuspwn vulnerabilities could be leveraged by malware and ransomware, the Microsoft 365 Defender Research Team said.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards












_(1).jpg&h=140&w=231&c=1&s=0)



