The top US spy agency actively worked to discover weaknesses in mobile phone networks worldwide and introduce new vulnerabilities to exploit them for surveillance, new leaked top secret documents reveal.

Former National Security Agency (NSA) contractor Edward Snowden is once again the source of the documents, given to the The Intercept.
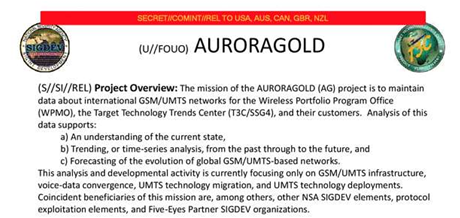
Some 1200 email accounts belonging to large mobile phone network operators were intercepted under Operation 'Auroragold' by the NSA, the documents dated 2011 state.
NSA tasked two special surveillance units - the Wireless Portfolio Management Office and the Target Technology Centre - with keeping track of encryption technology upgrades for cellular networks in order to bypass them. By May 2012, the NSA appear to have had technical information on 70 percent of worldwide networks.
The agency also actively targeted the GSM Association, a mobile industry organisation, to monitor its work in order to discover and exploit security holes, the documents state.
In particular, NSA attempted to capture IR.21 [pdf] documents shared by telcos. IR.21 documents form part of telcos' roaming agreements with each other, and detail the type of encryption used to protect customer privacy, along with technology upgrades on networks.
The NSA also appeared to have tried to introduce new vulnerabilities "where they do not yet exist", according to a leaked deployment planning slide.
Operation Auroragold. Source: The Intercept.
'Auroragold' information was shared with intelligence agencies in Australia, New Zealand, United Kingdom and Canada under the Five-Eyes agreement, according to the document.
The Australian Signals Directorate has been active in tracking overseas dignitaries' mobile phones and was revealed to have handed over confidential communications between a US law firm and the Indonesian government during a trade dispute in 2013.
Some 1.8 million encryption keys are said to have been captured by the ASD from Indonesian telco Telkomsel, earlier document leaks by Snowden show.
The 'Operation Auroragold' leak comes as a US senator today introduced a bill to stop the US government from build backdoors or security vulnerabilities into software and hardware.
The Secure Data Act states that government-driven technology mandates to weaken data security for law enforcement purposes would "compromise national security, economic security and personal privacy".
"The recent proposals from US law enforcement officials to undercut the development and deployment of strong data security technologies by compelling companies to build backdoors in the security features of their products work against the overwhelming economic and national security interest in better data security," the explanatory page [pdf] of the bill states.
"Moreover, the decision of government officials to repeatedly mislead the American public about domestic surveillance activities has resulted in an erosion of public trust.
"Requiring computer hardware and software companies to now create intentional gaps in their data security products to facilitate further government access to personal data will undermine the effort to restore trust in the US digital economy."



.jpg&h=140&w=231&c=1&s=0)







 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



