A security researcher updated a technique he devised a decade ago to create a browser-based attack that tricks network address translation (NAT) devices and firewalls to provide remote access to services on victim machines not normally reachable via the internet.
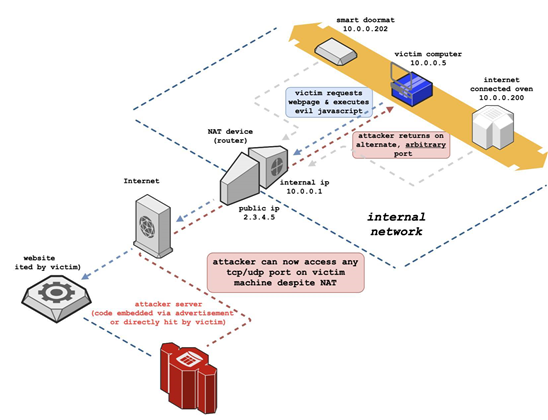
Samy Kamkar's NAT Slipstreaming attack requires support for Application Level Gateways (ALGs) proxies.
ALGs are commonly used to track connections between inside and outside network services, to allow NAT traversal for common protocols such as voice over IP telephony,
NAT is used to share a single public internet protocol address with multiple systems on an internal network which usually cannot be reached directly from the outside world.
Although not a security feature per se, NAT makes it harder for attackers to reach vulnerable systems on internal networks.
Kamkar's multi-stage attack exploits web browsers such as Chrome to load malicious code that is able to discover internal IP addresses via the Web Real Time Communications (WebRTC) protocol on victim machines.
For browsers that don't reveal IP addresses via WebRTC like Apple's Safari, or ones that don't support the protocol such as Microsoft Internet Explorer 11, a web-based transmission control protocol timing attack can be performed to map the internal network of the victim.
Once the IP address is known, a chain of other attacks are performed to generate a Session Initiation Protocol (SIP) registration packet for VoIP call set up.
The SIP packet has an internal LAN IP address to trigger ALG connection tracking, allowing the attacker to open any TCP or UDP port on victim systems remotely.
"[An] attacker can now bypass victim NAT and connect directly back to any port on [the] victim's machine, exposing previously protected/hidden services," Kamkar wrote.
For now, the only way to prevent remote NAT Slipstreaming attacks that establish malicious two-way communications into internal network services is to disable ALG, Kamkar said.




.jpg&h=140&w=231&c=1&s=0)






 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



