The IT security landscape changed dramatically last year, posing new and difficult challenges for developers that wish to protect users from having their data accessed by unauthorised entities.
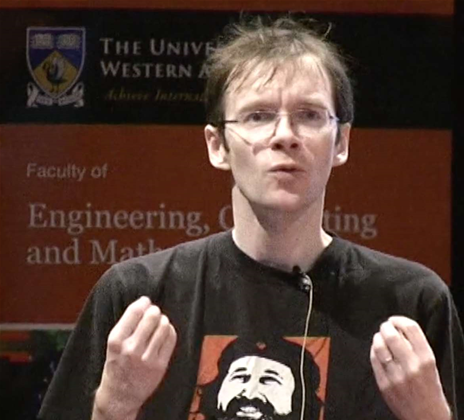
In this new reality, "the things we've been talking about as being theoretically possible were in fact happening," Linux kernel developer Matthew Garrett told attendees at his keynote address to Linux.conf.au in Perth, referring to NSA documents leaked to the public by whistleblower Edward Snowden.
"Governments of multiple nations are engaged in advanced technological attacks on their poulation, in order to, nominally, improve national security," he said.
The attacks against hardware were not vendor specific, he noted.
"There is no direct evidence that that the entire stack has been subverted - we don't know if there's a generic attack that the NSA can use," he said.
Garrett told the audience that in his area of expertise, Microsoft was one of the few organisations providing the right balance between security and user freedoms.
Garrett, who currently works for cloud hardware company Nebula, told his fellow open source advocates that a key protection measure built into the Unified Extensible Firmware Interface (UEFI) - which provides the first step in starting up computers - was deployed correctly by Microsoft, but not by Google and Apple, both of which are avowed Open Source users.
UEFI Boot verification - a controversial measure that can lock out unsigned code - is a must to protect users, Garrett said.
Operating systems are too complex to be perfect, he said, and computers need protection for their underlying software layers to prevent user devices from suffering persistent malware infections that are almost impossible to remove.
But users must also be armed with the freedom to modify and run the code they want without having to choose between that flexibility and security, Garrett told attendees. He noted that in this particular area, Microsoft had done the right thing.
"Microsoft has ensured that people buying PCs can have security and freedom to choose simultaneously", Garrett says.
On PCs certified for Windows 8, users can swap out the digital keys used to sign UEFI boot code. While this is not easy or straightforward, Garrett notes that this is not possible on devices running Google's Android operating system, or Apple's Mac OS X or iOS.
Cloud safety a trade off
Staying safe in the cloud is not easy either, Garrett noted.
"If you host with say Amazon, you have no way of knowing what else is running on the machine you're on," he said.
Hypervisor isolation is the only defence against malicious guests on virtual machines, Garrett said.
Cloud vendors must tell customers what they do to keep their clouds secure and - once again - user freedom must not be removed in the name of security, Garrett said.
"We have often assumed that one has to be at the expense of another, and that's not true," he said.
"We need to push back against that," he concluded.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026











_(1).jpg&h=140&w=231&c=1&s=0)



