Enterprises with Android devices risk having their networks compromised by a rapidly spreading Trojan Horse, according to researchers.
First discovered at the end of August by Check Point Software, the "DressCode" malware has been quietly spreading since at least April this year, according to security vendor Trend Micro.
Trend Micro mobile threat response engineer Echo Duan said the security vendor had found DressCode in over 400 apps on the official Google Play store. In its August report, Check Point said DressCode was embedded in more than 40 apps on Google Play.
The malware is found in several types of apps, including games, skins and themes for Android, as well as phone optimisation utilites, many of which have been installed hundreds of thousands of times.
In total, Trend Micro said it had found "DressCode" in at least 3000 apps. One reason the Trojan is so widespread is that the malicious code forms only a small part of the infected app, and therefore is difficult to detect.
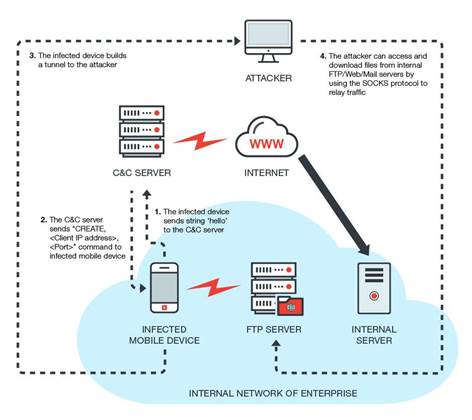
"DressCode" communicates with a command and control server after installation and sets up sockets secure (SOCKS) proxy to relay traffic between attackers and the internal network servers that the compromised device connects to.
This allows the malware to bypass network address translation (NAT) which would normally prevent direct connections from the internet to internal enterprise networks with non-routable private addresses.
Apart from intercepting data, Trend Micro said "DressCode" can be used to build botnets that are set up to conduct large-scale distributed denial of service attacks, click-jacking for advertising fraud, and compromising networked cameras.
The security vendor suggested Android device users take precautions like applying updates, being careful with the apps they install, minimising the use of public wi-fi and not "rooting" or bypassing the security lock-downs on their smartphones.
Google has been notified about the Trojanised apps and removed many of them from the Play store, the security vendors said.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards












_(1).jpg&h=140&w=231&c=1&s=0)



