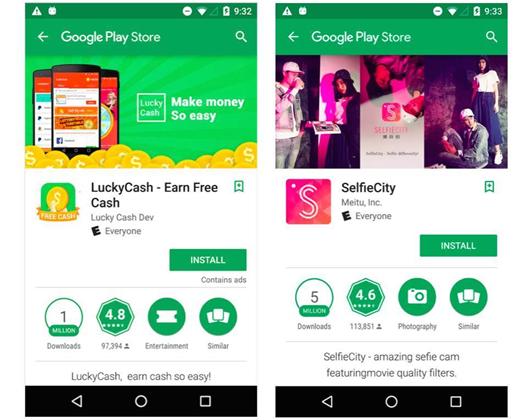
More than 500 apps have been yanked from Google's Play Store after they were found to contain a software development kit (SDK) that could download malicious plug-ins at will.
The SDK is used by developers for in-app advertising, and is made by Chinese vendor Igexin.
It has been used in hundreds of games, weather, internet radio, image editor and other apps, which have been downloaded in excess of 100 million times.
Security vendor Lookout discovered that the Igexin advertising SDK could download and execute plug-ins capable of spying on users, and alerted Google to the threat.
So far, the plug-ins found by Lookout have exfiltrated users' phone call logs. The data captured includes call lengths and the number dialled, as well as if the phone is is idle, ringing or off the hook, Lookout said.
As the malicious download capability was not created by developers using the SDK and not activated when the app was submitted to the Play Store, the threat was not detected by Google.
Lookout said the malicious functionality was fully controlled by Igexin, which could activate it at any time and download malware from a remote server controlled by the Chinese company.
The Igexin SDK appears to have been recognised as malicious since 2015, with security vendors such as Symantec adding detection for it then.
After being notified by Lookout, Google pulled more than 500 apps that feature the Igexin advertising SDK.
Google said it has improved security in its Android 8.0 operating system, which stops hostile downloader apps from operating without permission.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



