Handset maker turned security vendor BlackBerry has released technical documentation on how to run a stripped down version of the macOS operating system ARM64 kernel for Apple Silicon, for debugging and vulnerability discovery.
Apple last year released its first non-Intel based M1 chips, based on the ARM architecture, which BlackBerry says created difficulities for security researchers hunting for bugs on the new platform.
By using a modified version of the open source QEMU emulator that supports Apple's XNU kernel, patching and manually updating files, BlackBerry researchers made headway into running the fundamental piece of software that underpins the macOS operating system.
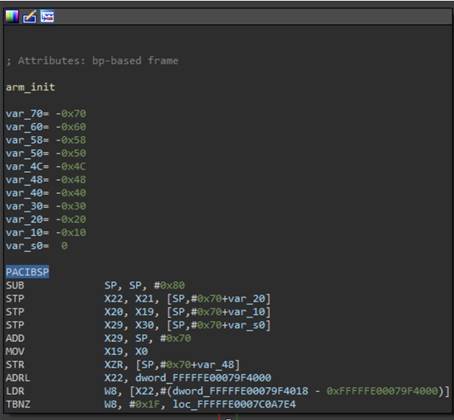
However, further work disassembling the macOS ARM64 kernel using the IDA 7.5 program was required.
As the open source XNU Darwin kernel for macOS contained no debugging symbols, BlackBerry researchers had to manually name functions one by one over the two-month period of research and testing, reading plain ASCII text strings for cues.
Describing the two-month process of getting to a bash command shell prompt after the kernel had booted up as "gruelling" and "anything but straightforward", the BlackBerry researchers worked their way through source code and achieved a functioning emulation that can mostly accept system commands.
Support for hard disk and other features still awaits implementation, and the shutdown command crashes the emulated system.
"Yes, that is a panic at the end. Add “fatal shutdown” to the list of issues awaiting a fix," the BlackBerry researchers said.
Apple has in the recent past taken a dim view of efforts at running its software under virtualisation for security research purposes.
The hardware and software giant took emulation vendor Corellium to court for copyright infringement for creating a virtualised version of the iOS operating system for mobile devices, but lost the case last year.











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



