The federal government is, and realistically should be, the benchmark for cyber security in Australia.

It has the most to lose, holding not only our most sensitive state secrets, but also managing air traffic control, billions of dollars in welfare payments, and databases of financial details for each and every one of us.
Canberra took a big step forward in 2013, making the Australian Signals Directorate’s ‘Top 4 Strategies to Mitigate Targeted Cyber Intrusions’ a mandatory part of the Australian Government Information Security Manual.
The ASD boasts that these four strategies - application whitelisting, patching applications, patching operating systems, and minimising who has admin privileges - will defend against 85 percent of all successful intrusions it sees every year.
Earlier this year ASD infosec chief Major General Stephen Day said the checklist had even been adopted internally by security software giant Kaspersky.
So what is the state of security within the Australian government really like?
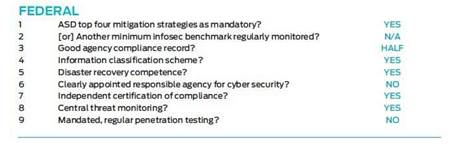
Score: 5.5/9
The answer to this question is only truly known by a handful of national security mandarins with extremely high security clearances.
Publicly, the ASD and its partners at the Australian Cyber Security Centre (ACSC) insist things are getting better, identifying 2012 as a turning point.
The ACSC’s recent threat report said while “the overall number of cyber security incidents increased in 2014, the number of confirmed significant compromises of federal Australian government networks has decreased since 2012”.
While the government-wide mandate for the ASD top four strategies is a positive step, the national auditor concluded that even the most IT-heavy Canberra agencies didn’t have a hope of reaching full implementation by the government’s June 2014 deadline.
The Australian National Audit Office (ANAO) has taken it upon itself to audit each and every federal agency against the top four on a rolling schedule.
It has already looked at seven agencies, including the Tax Office, Human Services, Customs and DFAT. The Australian Federal Police, Communications and Agriculture departments and AUSTRAC are next in line.
Patching has emerged as a major issue. The ISM demands that critical security patches are applied within two days of their release. In its first audit, the ANAO found that not one of the seven agency behemoths investigated had achieved this.
DHS CIO Gary Sterrenberg questioned how realistic this sort of demand was for an agency of its size - the DHS patches its 2.5 million devices according to 30-day rotation, so at any given point some will be out of date.
Some of the flaws the ANAO discovered, however, were less forgivable - like agencies running AppLocker for whitelisting but never switching out of ‘audit mode’, meaning none of the rules were actually being enforced by the software, just monitored hypothetically. Three of the seven agencies had not applied any security patches between May and August 2013.
The end game here is clearly to have all federal agencies complying with the ASD top four. But what happens then?
As one infosec expert pointed out, once we “drain the swamp” of the easy vulnerabilities, the hackers will get better and inevitably the strategy’s 85 percent success rate will dwindle.
Another pertinent question for the future is - as Canberra shores up its security protocols, will opportunistic cyber assailants be forced to look elsewhere for sitting-duck targets?
And are our states and territories ready if they are the next targets on the list?
Want to see how all the states and territories stack up? Download our State of Security report. Do you work for the government? Let us know how you would have scored your state here.












 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



