Microsoft is strongly urging customers with Exchange Server installations to apply patches that address critical vulnerabilities currently exploited by Chinese nation state hackers to steal information and install malware.
The urgent patches were released out-of-band to address an attack chain affecting Microsoft Exchange Server versions 2010, 2013, 2016 and 2019.
Four new zero-day vulnerabilities are being exploited by the Hafnium state-sponsored group to get access to Exchange Servers, Microsoft said.
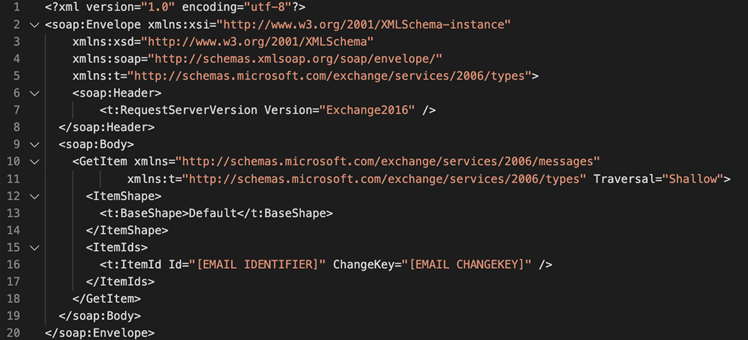
These include the CVE-2021-26855 server-side request forgery flaw that allows attackers to send arbitrary hypertext transfer protocol requests from untrusted sources to port 443, and authenticate as the target Exchange Server.
Hafnium is also exploiting an insecure deserialisation issue in the Exchange Unifiied Messaging service to run code as the high-privilege Windows SYSTEM account, and two file-write vulnerabilities post-authentication, Microsoft said.
Once they have gained initial access with the above attack chain, the Hafnium hackers deploy web shells on the compromised Exchange Servers to exfiltrate email account and other data, and perform other malicious activity.
Security vendor Volexity, which found evidence of attacks on January 6 this year, has dubbed them 'Operation Exchange Marauder', and says the vulnerabilities are easy to exploit.
"This vulnerability is remotely exploitable and does not require authentication of any kind, nor does it require any special knowledge or access to a target environment," the Volexity researchers said.
The attacker only needs to know the server running Exchange and what account from which they want to extract email.
Even so, Volexity rates the attackers as highly skilled and innovative in their ability to bypass defences and get access to targets.
Until the patches have been applied, Volexity is urging organisations to temporarily disable external access to Exchange Servers.
Microsoft has observed Hafnium attack United States-based organisations such as infectious disease researchers, law firms, tertiary education institutions, defence contractors, policy think tanks and non-government entities.
Office 365 and Exchange Online are not vulnerable to the current zero-days.



.jpg&h=140&w=231&c=1&s=0)



_(39).jpg&w=100&c=1&s=0)



 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



