Microsoft is warning users that new, critical remote code execution bugs affecting all current versions of Windows is being actively exploited.
The vulnerabilities lies in the Windows Adobe Type Manager Library, and can be exploited with malicious Adobe Type 1 Postscript format multiple master fonts, now superseded by OpenType fonts.
Attackers can exploit the vulnerabilities in several ways, by embedding the Type 1 fonts into documents and convincing users to open them or look at them in the Windows Explorer preview pane, Microsoft said.
Windows version 7, 8.1, RT 8.1, 10 are vulnerable to the remote code execution flaws, along with Windows Server 2008 service pack 2 onwards.
On vulnerabile Windows Server variants, the default Enhanced Security Configuration does not mitigate against the vulnerabilities, Microsoft warned.
Although the vulnerability is rated as critical, Microsoft said that for systems running supported versions of Windows 10, a successful atack could only result in code execution within an AppContainer sandbox content, with limited privileges and capabilities.
AppContainers are security features that mitigate against risk by limiting applications' access to Windows system areas and resources.
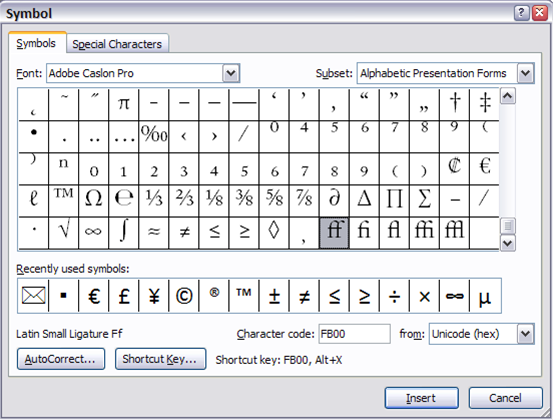
There are currently no patches available for the Adobe Type Manager Library vulnerabilties, but Microsoft suggests that users disable the Preview and Details panes in Windows Explorer as a workaround.
This prevents the automatic display of OpenType fonts in Windows Explorer which could trigger the vulnerability.
Disabling previews does not however prevent local, authenticated users from running malicous programs that can exploit the vulnerability.
A second suggested workaround by Microsoft involves disabling the Windows WebClient service using the Services.msc Microsoft Management Console tool.
This blocks what Microsoft says is the most likely remote attack vector, through the Web Distributed Authoring and Versioning (WebDAV) client service.
Even though attackers can still exploit the vulnerability to run programs located on targeted computers or local area networks, users will be prompted for confirmation before arbitrary programs from the internet are opened, Microsoft said.
A third workaround involves renaming the Windows OpenType and Type 1 font driver dynamic link library file, ATMFD.DLL.
Doing so could cause third-party applications that use OpenType fonts from working properly, Microsoft warned.


.jpg&h=140&w=231&c=1&s=0)








 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 Forrester's AI Forum Sydney
Forrester's AI Forum Sydney
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



