Microsoft was hit with a pair of unwelcome security reports late this week.
The company released a fix for a vulnerability in Windows Server 2000 shortly before a security researcher posted details about a new flaw in Windows 7.
Researcher Laurent Gaffie said that the vulnerability could cause a denial of service, crashing the targeted machine by executing an infinite loop.
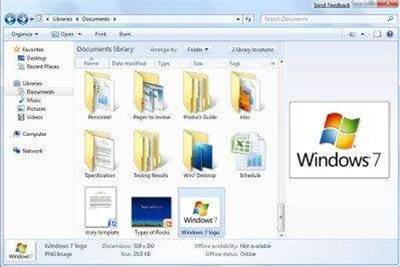
The flaw is said to exist in the server message block (SMB) component of Windows 7. Gaffie suggested that the vulnerability could be triggered through Internet Explorer and could allow an attacker to bypass firewall protections.
In reporting the details on the vulnerability, Gaffie took time to mock Microsoft's security policies, namely its secure development lifecycle (SDL) programme.
"This bug is a real proof that SDL #FAIL," the researcher wrote in a blog posting.
"The bug is so noob, it should have been spotted 2 years ago by the SDL if the SDL would have ever existed."
Disclosure of the flaw comes as Microsoft has issued a patch for another vulnerability in Windows Server 2000.
The company said that the vulnerability lied within the License Logging Service (LLS) within Windows 2000 and was given Microsoft's highest severity rating: 'critical'.
If exploited, the company warned that the flaw could allow an attacker to remotely access a server through an anonymous network connection and trigger a memory error which may allow for remote code execution on the targeted server.
The company said that Windows Server 2008 was not vulnerable to the flaw.




.jpg&h=140&w=231&c=1&s=0)





.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



