First State Super has dropped legal threats against security consultant Patrick Webster for disclosing a security hole without authorisation.

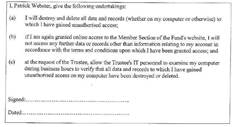
The company had served Webster with a legal document (pdf) which demanded he provide the company's IT staff access to his computer.
First State Super was concerned Webster had kept a store of customer data obtained after he demonstrated a direct object reference vulnerability in the fund's website, through which he accessed 578 accounts using a script.
Webster, a consultant who was formerly a security professional in the NSW Police, went public to Risky.Business and SC last week.
"There has recently been some media coverage about unauthorised access to our members’ online benefit statements. The members whose statements were viewed have been notified," a statement from First State read.
First State Super reported the issue to the NSW Police to "ensure that any unauthorised copies of the member statements involved were destroyed".
"We have no doubt that First State Super members would expect such certainty in relation to the privacy of their information," it said.
The NSW Privacy Commissioner was investigating the security flaw. It appeared unlikely that an undertaking would be imposed on First State Super because it patched the vulnerability immediately and informed customers.
First State Super said it "appreciates" Webster's disclosure and had "no intention of taking any other action against him".
But it wasn't the first or the last company to threaten Webster.
During recent security tests with his consultancy OSI Security, Webster discovered holes in a rival information security firm's content management system (CMS).
Webster discovered a bypass of the CMS web log in. He advised the company immediately at about 11pm because administrative pages could be trawled by search bots.
"The next day their email system had crashed," Webster said. "I guess the staff thought I had something to do with it. They threatened to call the police."
This time the situation was quickly defused and the vulnerability was fixed.
Security testers will continue to face threats for disclosing vulnerabilities to unprepared businesses.
Penetration testers Chris Gatford and Drazen Drazic said security professionals are inherently inquisitive and must balance the desire to help fix bugs with the risk of litigation.
Webster said he would thoroughly evaluate this risk but did not rule out future unauthorised disclosures.

.jpg&h=140&w=231&c=1&s=0)








.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



