IBM has attributed its recently publicised decision to ban Apple's assistant feature Siri on employee-owned iPhones to concerns surrounding leakage of sensitive data.
The computing giant's chief information officer Jeanette Horan told MIT's Technology Review in a recent interview that the company's bring-your-own-device strategy for its 400,000 employees required employees to avoid potentially insecure or external applications.
The company had decided to ban the Siri feature due to IBM's "extraordinarily conservative" security mindset, Horan said.
Bowman Hall, IBM's worldwide director of cloud client computing engagements, told attendees of the company's Pulse conference in Sydney this week that data leakage remained a prevalent concern as employees within its ranks adopted cloud services without the permission of IT.
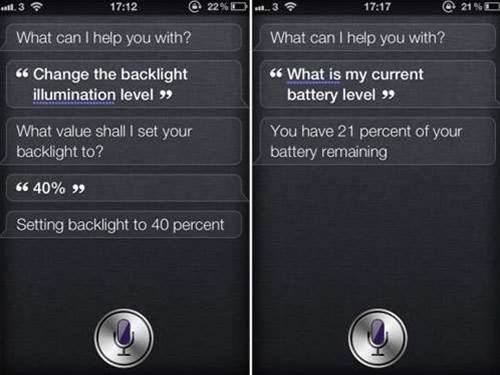
"If you were to take an iPhone with Siri and say 'show me the email with our current sales forecast numbers', that data goes up to a server at [Apple], crunches some analytics and Siri would say 'you're on track' or whatever Siri would say," Hall said.
"That's corporate data, via Siri, going up to Apple servers. That's not something we at IBM want."
Hall recounted similar fears among clients noting that the CIO of a major US drug company had voiced concerns over how staff could upload sensitive patient research data to a public cloud service like Amazon in order to analyse and store it.
Those moves by employees contravened standard IT security practices and were largely borne out of an unwillingness to wait the months technology teams could take to provision the required infrastructure.
Hall pointed to Dropbox as an example of another consumer cloud service banned within IBM's walls.
"What we have to do is we have to respond and give our employees the same capability that Dropbox provides," he said.
"Because if we don't, they're going to use Dropbox anyway. And we know that, so we have to prevent from happening from a reactive standpoint and from a proactive standpoint offer that capability ourselves."











 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



