A misconfigured data transfer server left sensitive data from big name car makers and their employees wide open to the internet, a security vendor has revealed.
Canada's Level One Robotics, which provides automation services for global companies such as VW, Chrysler, Ford, Toyota, Tesla and ThyssenKrupp, is at the centre of the incident.
The company uses the open source rsync data transfer and synchronisation utility to mirror information across internet-connected servers.
However, researchers at Upguard discovered and made public that Level One's Robotics rsync setup did not limit which clients could access it.
This meant anyone who could connect to the rsync server at Level One Robotics and download the data it stored.
All in all, some 157GB of sensitive information was left exposed by Level One Robotics.
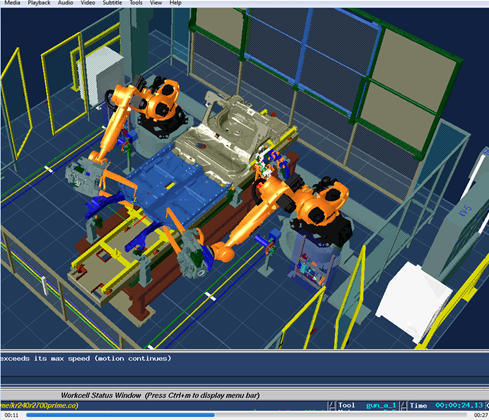
This included customer data such as factory plans, assembly line schematics, robot configurations, identity badge requests and virtual private networking access forms, along with non-disclosure agreements.
Ford Thailand, Toyota Canada, GM, KUKA, Pratt & Whitney, Tesla, and VW Group of America are some of the big name manufacturers whose data was left exposed.
Upguard also found sensitive Level One Robotics data for employees, including scans of passports, driver's licenses and other identification.
Level One Robotics' corporate data was also included in the rsync collection with invoices, price lists, insurance polices and other enterprise business documents stored on the server.
Not only did Level One Robotics not limit access to the rsync server, but it was also configured to allow anyone write to it as well.
This left files stored on the rsync server open to manipulation and alteration.
Upguard said bank account numbers for direct deposits could have been changed in business documents, or malware planted in the files on the server.
The insecure server was discovered by Upguard on July 1, and Level One Robotics closed off access to it on July 10.
Neither Upguard nor Level One Robotics have said how long the rsync server was left exposed, or if there was any unauthorised access to it.




.jpg&h=140&w=231&c=1&s=0)






 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



