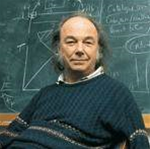
After the imposing quadrangle of Royal Holloway's original buildings, Fred Piper's office is a stereotype of academic muddle, complete with chairs piled deep with papers and a wall-long blackboard covered with almost illegible scrawls. Piper himself is jolly, with casual clothes and uncontrolled hair. He is also as sharp as a razor and, although softly spoken, makes his points with rapid-fire precision.
That we are in an academic environment is very apparent. While we talk, students breeze in and out, asking about coursework and lectures, and colleagues pop in to drop off notes. But the brief interruptions also provide clues to the depth of the department. Many of the students are employed at top firms, there to become security specialists at the top of their profession. And among the colleagues stopping by is John Austen, formerly head of Scotland Yard's Computer Crimes Unit and now part of Piper's teaching team.
The irony is that, despite this continuous activity, Piper recently took retirement – officially at least. In practice, he is still very much involved in the Masters course in computer security that he created at Royal Holloway 15-odd years ago, and which has an unquestioned international reputation for excellence.
Like many security specialists, particularly those in academia, Piper's roots are in mathematics, from where he expanded his interests into cryptography and then security in the whole, after a communications manufacturer turned to him for help.
"I was a mathematician and a mathematics professor. And a company called Racal-Comsec phoned up and said they needed to hire a mathematician because their engineers were no longer capable of assessing the security of their cryptographic algorithms. They used to do that just by testing it, but now they needed some theoretical proof of assurance and security. And a research student of mine, Henry Beker, got the job." Beker is now a visiting professor at the Royal Holloway Information Security Group, one of several ex-Racal staff on the group's roster. "There was very little published about cryptography at the time (this was in the 1970s)," and so Piper became involved in cryptography, as others with backgrounds in mathematics have done. "I started off as a cryptographer, only interested in cryptography and mathematics, but then I sort of drifted into security."
A strong practical streak becomes apparent as we discuss crypto. "Cryptography is too narrow," he says. "Encryption by itself is useless. It is interesting, fascinating even, but if you don't use it right, what's the point of having strong algorithms?" That point shapes much of his thinking: "Even security is useless if you have nothing to secure," he continues. "So you have got to be involved in business. You've got to understand what you're developing, but also why it is developed and how it will be used."
Piper formed a consulting company of his own, Codes & Ciphers Ltd, in 1985. This, he says, was "mainly to understand what I was doing. Here we were producing the algorithms – I wanted to know how people used them, how they were misused, and what use they were. You soon realise that cryptography is a very small part of a very big subject."
So when he began working on the MSc course structure, it was with a bigger picture in mind. "The first decision was not to do a degree in cryptography," he says. The course was first launched in 1992, but that was preceded by five years of preparatory work.
"When we started this MSc, it was the only one in the world, and we had no syllabus to guide us. It took from 1987 to 1992 to recruit the right people, and for us to get the right skills. We didn't want to be academics telling industry what to do, we wanted to involve industry in our course."
From the early days, Piper has kept Royal Holloway's security course strongly connected to the information security industry. The staff are mostly from business, rather than academic, backgrounds, and industry specialists make regular lecture appearances. And many of the course's students are already employed in the IT industry, from technical sectors and management, so the material must be tailored to that audience.
Since its inception, the course has become popular while the information security market has ballooned. From its initial launch to just seven students, the department reached its target of 30 students in its second year. After that, the number of applicants kept growing, recalls Piper, to a peak two years ago of 240. Along the way, Piper's department won the Queen's Anniversary Prize for Higher and Further Education in 1998.
The course now has 170 classroom students and more than 100 participating via distance-learning. The limit now is largely physical, with constraints imposed by the size of available lecture theatres and lab space.
But while there has been a sharp growth in the number of specialist certifications such as CISM and CISSP, and the launch of dozens of vendor-specific security courses, a relatively small number of universities have stepped up with similar programmes.
Most of the courses available are security modules as part of programming or computer science degrees, or in the mathematically-oriented fields of cryptography, while others focus on single areas such as Cranfield University's Masters in Forensic Computing.
This might change in the near future: universities have recently been criticised for not including sufficient security training in their existing computer science and related courses.
The SANS Institute surveyed several US institutions and found many with no security modules at all. And at the SC Conference in October, Simon Perry levelled similar criticism at one UK college which, he said, did not have "a single security lecture in its entire computer science (CS) course."
Although Piper believes this does not necessarily indicate a failure in universities (he points out that CS courses vary widely in focus: some purely dedicated to programming, while others are entirely theoretical), he agrees some need to do more. But, he says, many underestimate the amount of effort involved in setting up a credible security course.
"If you want the degree, you've got to have the experience. You've got to have people who are respected by the industry. And credibility has to be given to you – it's not something you can just go and get." He also says most universities are taking steps to include more awareness of security into their curricula. "At least I hope so," he says. "It seems to be moving that way."
Piper is critical of industry courses such as the CISSP, but believes they are valuable within a certain context (he has been the recipient of both honorary CISSP and CISM qualifications). "You can't learn what we teach in books. If you haven't got the practical experience then what have you got? [CISSP] gives you a background, and we encourage our students to do it. After they have done our course, they can take the exam and become 'Associate CISSPs'. But in terms of knowledge, I don't think anyone would deny that we are more testing in terms of content and in the manner of examination. A multiple-choice exam [such as the CISSP's] is junk."
The Royal Holloway course is not for everyone, he hastens to add. "The world does need security specialists, but they don't all need MScs. They don't even need degrees. And there are two deficiencies in any degree – first, you can't take it away, and second, they don't imply any practical experience." Certifications, whatever their other downsides, do address those particular questions.
With the reputation of Royal Holloway's course and its professors established in the industry, government and industry bodies began to turn to them for guidance as well. Piper and several of his colleagues are active consultants, working closely with industry bodies, government committees, standards groups and others. "If you run a degree like this, then you have to consult. If we don't consult, we won't have the touch with the industry. And if the industry don't know you, they won't trust you."
Piper has consulted to, among others, the financial industry and the government in various roles. He is currently a member of a DTI Foresight panel, looking at information technology crime and fraud.
Drawing analogies to his work with financial companies, Piper says that the information security industry must reach similar levels of assurance for businesses to make progress. Shopping online with creditcards is not wholly safe, but the creditcard companies have clearly demarcated lines of liability and responsibility. "The business has said: never mind the security, we'll accept the risk!" One of the perceived risks, loss of reputation, is vastly overstated, he says, recalling an incident with an ATM network where an institution had been the victim of duplicate "white" cards and feared a public backlash.
"It held a press conference, and had me on standby on the phone in case of any technical questions. But I missed it, and asked the fellow afterwards what had happened. He said [the press and public] had barely even noticed."
Understanding the risks, and potential costs to business, is implicit in good security, a point Piper makes vigorously and often. "If you run a corner shop and lose five quid a day to shoplifting, you aren't going to pay a security guard £100 a day to stop it." Nor will changing the law be the answer, he says, pointing to the ineffectiveness of anti-spam legislation, although he does respect the efforts of the National High Tech Crime Unit, which he describes as "under-resourced, but doing a bloody good job".
In the light of an increasingly legislation-happy administration, his opinion of government is rather low. Low enough to be unprintable, in fact, although there is more humour than antipathy in his pronouncement. Social change, he says, is the only real solution.
"To sound idealistic, we need cultural change. It is slowly happening. People are beginning to accept that hacking is a bad thing. Hackers used to be heroes, but now I think people are realising that there is a danger in certain types of irresponsible hacking. So attitudes are changing. The laws may not change, but attitudes change. Should ISPs be responsible for data on their networks? There are moral issues in there you can debate forever. Law is the last fallback. You do need it sometimes, but it is very hard to enforce."
Meanwhile, the industry will keep making the same mistakes, believes Piper. New technologies will arrive, introducing vulnerabilities, and the security people will be called on to plug the holes. "If you look at the vendors – Microsoft, for example, they have a monopoly and we rely on them. And they do provide a lot of services, but inevitably there are vulnerabilities and we have viruses and worms – we are vulnerable.
There have been improvements, but that rather depends on your point of view." Similarly, IS problems become security problems when it threatens one of the three pillars of information security: confidentiality, integrity and accessibility. Spam is really just an email management problem, he says, but if it impacts on a user's ability to access his email, it must become a security priority.
The ebb and flow relationship that exists between security, IT, industry and government ensures the importance of educational institutions to the business world, both in training experts and offering an independent view. It's a role Piper will not relinquish willingly.
Though he has just retired after more than 15 years at the helm, his retirement is largely symbolic. Primarily, "retirement" seems to involve giving up anything that resembles administration. He remains closely associated with the university, and will be taking a more public role, involving speaking and publicity, rather than lecturing.
He is also a trustee at Bletchley Park, working to preserve the history of cryptography and security with projects like the rebuilding of Colossus, the codebreaking computer created during World War II, although as the founder of the world's first Master's programme in information security, his own place in history is already staked out.
For more information about the Royal Holloway's Information Security Group, visit www.isg.rhul.ac.uk










 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



