David Jones and Click Frenzy suffered a series of e-commerce glitches as they attempted to run separate national online shopping promotions.
Fairfax reported as early as 10.38am AEDT on Tuesday that a "technical glitch" was locking some shoppers out of particular promotions on David Jones' website.
The paper quoted a spokeswoman for the retailer saying that the glitch was unrelated to increased traffic volumes.
However, hours later, the site had to be pulled offline completely, forcing David Jones to apologise on social media channels.
"We are currently performing some urgent fixes to our online store to resolve the performance issues we're experiencing during our Christmas Frenzy event," David Jones reported on its Facebook page just after 2pm.
The site was inaccessible for three hours, with the retailer advising at 5.10pm that the site had been reinstated.
Tests by iTnews shortly after confirmed the site was functional but experiencing significant latency loading web pages.
Several commenters ridiculed the retailer for the site's capacity and performance issues.
David Jones ran its online sale ahead of the start of Click Frenzy, a wider online shopping initiative that it is not participating in.
The Click Frenzy site did not fare much better, becoming inaccessible minutes into the promotion.
Its operators initially slammed critics on Facebook, one of several social media outlets that prospective customers turned to, to vent against the unavailability of the site.
"Click Frenzy is far from embarrassed!" it noted in a Facebook post, while acknowledging the site was inaccessible to "some individuals".
However, it was later forced to acknowledge there were more serious issues when the site remained inaccessible more than an hour-and-a-half after launch.
"Firstly, I would like to issue an apology to anyone who has been inconvenienced and frustrated by the technical issues relating to the inaugural Click Frenzy 24 hour online sale," organiser Grant Arnott posted.
"The technical directors, developers and infrastructure specialists involved in this inaugural event are working to get to the root of what occurred with the wave of traffic at 7pm.
"I am not in a position to describe exactly what has occurred yet as the teams involved are working on the solution first to resolve any problems.
"We will provide answers as soon as they are available. We will continue to issue updates."
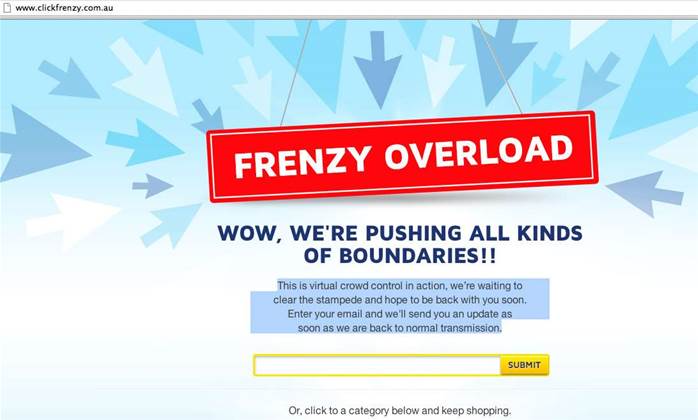
By 9.55pm, the site was serving a placeholder message asking users to register to be alerted when it returned to full service.
"This is virtual crowd control in action, we're waiting to clear the stampede and hope to be back with you soon," it read.
"Enter your email and we'll send you an update as soon as we are back to normal transmission."
The site appeared to regain full functionality after midnight AEDT Wednesday.
Click Frenzy's web host, UltraServe, said in Twitter posts it was experiencing "huge volumes of traffic as expected" and that it was "prioritising users", although it did not elaborate.
"We cracked 2 Gbps of non-image content which is quite significant," the host said.
UltraServe said that other customers had not been affected by the flood of traffic caused by hosting Click Frenzy.











 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



