University researchers claim to have designed a 'nearly unbreakable' cryptography model based on the human respiratory system, which they say could make life tough for criminals and spying governments.
The new class of secure communications was modelled off recent discoveries into the way the human heart and lungs coordinated rhythm information.
Three members of the University of Lancaster's physics department designed the system, which was described as "highly resistant" to attacks.
"This promises an encryption scheme that is so nearly unbreakable that it will be equally unwelcome to internet criminals and official eavesdroppers," the university's Professor Peter McClintock said.
Fellow researcher Dr Tomislav Stankovski said the novel encryption scheme built on the intersection between physics and biology was "radically different" from existing schemes.
"Inspired by the time-varying nature of the cardio-respiratory coupling functions recently discovered in humans, we propose a new encryption scheme that is highly resistant to conventional methods of attack," Dr Stankovski said.
The platform, the trio of researchers explain, uses biological coupling functions to offer an infinite number of secret encryption key choices making it "virtually impossible" for attackers to crack.
Several of these secure streams could be transmitted at once, enabling all of a users' devices to run on one encryption key instead of dozens of variants.
The system is "exceptionally resistant" to interference from random fluctuations -- or noise -- that affects communications systems, the researcgers claim.
That meant the system was useful for landline and mobile phones and a variety of wireless communications that endured a large amount of external interference.
"Our scheme is highly modular and is readily extendable to support far more complex and diverse communications applications than [those] examples," the researchers wrote in a paper (pdf).

They predicted the previously theoretical concept of coupling-function encryption would have a huge impact on many experimental implementations.
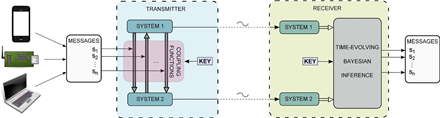
The researchers explained the crypto system in the above figure:
"A number of information signals coming from different channels or communications devices (e.g., mobile phone, sensor networks, or wireless broadband) are to be transmitted simultaneously.
Each of the signals is encrypted in a coupling function; i.e., they serve as coupling scale parameters in the nonlinear coupling functions between two self-sustained systems in the transmitter. Two signals, one from each system, are transmitted through the public channel.
At the receiving end, two similar systems are enslaved, i.e., completely synchronised, by the two transmitted signals. Finally, by applying time-evolving Bayesian inference to the reconstructed systems, one can infer the model parameters and decrypt the information signals. An important feature of the scheme is the private key holding information about the particular coupling functions in use - which, in principle, has an unbounded continuum of possible combinations.
The number of coupling functions in use will always be finite, depending on the specific number of information channels that are needed; the choice of forms available for the coupling functions (forming the private key) is, however, unbounded."


_(37).jpg&h=140&w=231&c=1&s=0)
.jpg&h=140&w=231&c=1&s=0)







 Melbourne Cloud & Datacenter Convention 2026
Melbourne Cloud & Datacenter Convention 2026
 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
 The 2026 iAwards
The 2026 iAwards












_(1).jpg&h=140&w=231&c=1&s=0)



