Up to 32,527 Apple Macs are infected with a trojan that has enslaved their machines into the massive Flashback botnet.

The attack exploited a nasty but recently patched Java hole to install the FlashBack Trojan on Apple OS X machines.
Apple released the important patch to close the Java security holes this week, trailing Oracle's patch issued in February, and Microsoft which also identified that attackers had built exploit kits and were bypassing the platform's sandbox.
The Java exploit was the latest evolution of Flashback which targeted Mac through Adobe Flash in 2011.
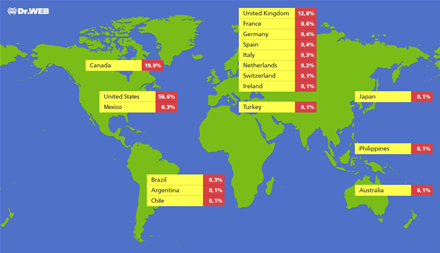
Russian security firm Dr Web claimed the Backdoor.FlashBack botnet had infected more than 550,000 machines, mainly in the US, the UK and Canada.
About 6 per cent of infections were located in Australia, but a recent update on Twitter by Dr Web analyst Sorokin Ivan suggested the number of infected machines had tipped 600,000.\
It should be noted that while the attack demonstrates the vulnerability of Mac machines to security threats, it pales in comparision to WIndows threats. Some botnets contained millions of infected Windows machines.
The number of compromised web sites infected with the trojan was unclear but thought to be large. Dr Web said "sources" had claimed up to four million pages were compromised by the end of last month.
It said dlink.com was reported on Apple forums to have hosted the malware.
Intego researchers said the malware had attempted to steal user names and passwords however Ivan refuted the fact, and said its goal was to hijack search traffic.
Dr Web said in a post that an executable was saved on compromised machines which downloaded and executed a payload from a remote server.
It searched hard drives for:
- /Library/Little Snitch
- /Developer/Applications/Xcode.app/Contents/MacOS/Xcode
- /Applications/VirusBarrier X6.app
- /Applications/iAntiVirus/iAntiVirus.app
- /Applications/avast!.app
- /Applications/ClamXav.app
- /Applications/HTTPScoop.app
- /Applications/Packet Peeper.app
If those files were not located the trojan would ping a list of control servers and would enable load balancing to distribute requests.
To count the number of infected machines, analysts at the Russian security firm located a unique identifier for each victim sent to the servers and sinkholed (pdf) the traffic to their boxes.
Mac users should apply the Apple Java patch, while those who suspect their machines were infected can follow F-Secure's removal instructions via Terminal.




.jpg&h=140&w=231&c=1&s=0)





 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026
 Security Exhibition & Conference
Security Exhibition & Conference












_(1).jpg&h=140&w=231&c=1&s=0)



