Service providers were obliged to defend their networks against security attacks but not to the point they became security police, Arbor Networks solution architect Roland Dobbins told an audience of ISPs today.
Speaking at the AusNOG conference in Sydney, Dobbins (pictured) argued that service providers had an opportunity to be "more proactive on their home turf" when it came to information security.
"Just as we have moral and practical obligations to defend our homes against fire, flood or intruders, we have to do the same for our networks [against threats from the internet]," he said.
"Service providers have to take basic measures to keep their networks up and running.
"Whether we like it or not, we have to do things to strengthen the network itself - [for example, to] filter out hostile traffic directed at our servers. You've got to defend your network. You can't just step back and say, 'I'm at Layer 2. I don't care what happens at Layers 3 or 4."

Could the NBN be a failed state?
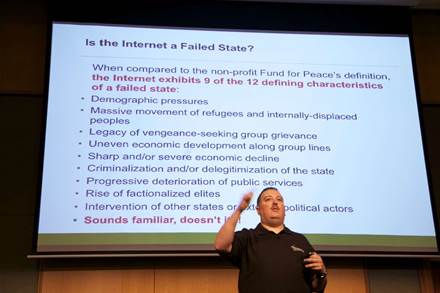 |
| Arbor Networks' Roland Dobbins at AusNOG, September 17, 2010. |
The internet met nine of 12 criteria to qualify as a "failed state", he said, so it was up to NBN Co to ensure its "brand new, large southern [virtual] continent" didn't fall into the same law-enforcement "cesspit".
"If the network isn't defensible and there's not an active push to impose law and order, there's a danger [the network] wil become a cesspit and fail," as it had in China and Russia where criminal hacking had taken the place of litigation in the West as part of "legitimate" business strategies, he said.
"We have to take positive action," he said, believing that an unmanaged network could rapidly become unmanageable, insecure and then un-securable.
"We don't want that at all," he said.
Dobbins said that a responsibility of governments was to "provide security and stability".
"NBN Co is essentially a Government-owned enterprise. In the public eye ... they see it as an arm of Government," he said.
"Whether that's true or not, people tend to expect more from their governments than they do from the private sector so the bar is set a bit higher.
"It's because of this perception that providing security and stability should be a primary purpose of NBN."
Dobbins said that NBN Co should set security standards in the acceptable-use policies imposed on retail ISPs and the interconnect standards for devices that connected to the network.
It must also "have the ability to marshal resources and be able to coordinate a defence of its infrastructure", he said.
He said NBN Co should write a "formalised NBN threat model" as a living document that was regularly updated.
He also called on NBN Co to contribute to the operations security community globally and urged it to install a chief information security officer with oversight of such issues as a matter of urgency.
Dobbins acknowledged that tackling security in the manner he suggested would involve developing an understanding of the traffic moving across wholesale and retail ISP networks.
But he said he was "not trying to advocate deep-packet inspection", nor did he want to "put NBN Co in the role of law enforcement".
"I'm not trying to say ISPs should be an enforcer," he said in response to a question from AusCERT general manager Graham Ingram.
"I'm saying that to keep a network up and running, there's an absolute minimum of self-defensive things that service providers should do.
"Service providers can be more proactive on their home turf and the NBN might be an opportunity to do it."











 iTnews Executive Retreat - Data & AI Edition
iTnews Executive Retreat - Data & AI Edition
.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards












_(1).jpg&h=140&w=231&c=1&s=0)



