Daniel Grzelak, an ethical hacker with IT security consultancy SIFT, told the AusCERT conference that infrastructure from power generators to water and waste supply were at the mercy of hackers because the industry won't take even basic security precautions such as passwords and authentication.
"From the hacker's perspective, you can do a lot of damage and for people controlling this stuff it's a lot of headaches and a lot of stuff to deal with," Grzelak said.
The internet offers a cheaper, faster way for utilities, infrastructure providers and councils to deploy smart devices such as power meters but these are seldom attended by even basic security systems, he said.
Worse, many such supervisory control and data-acquisition (SCADA) networks invite hacking by exposing too much information about their use and even offering web pages to control them.
Grzelak showed a public web interface that controlled a reactor:
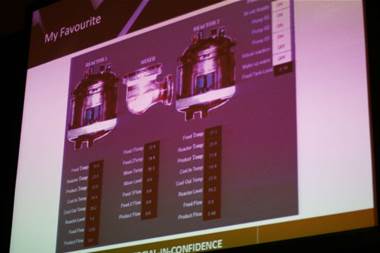 |
| A web interface for a reactor shown at AusCERT - Credit: Nate Cochrane |
"Why would you put a web interface on something that critical?" he said. "But everything released from now will have a web interface on it. The problem with web interfaces is ... you provide so much more information to an attacker that they didn't have beforehand."
That included product versions, system purpose, access instructions, status diagrams and point and click control that, Grzelak said, "hackers love".
Devices found on the web include electrical generators, meters, cameras, thermometers, ovens, water and waste utilities, he said.
Grzelak demonstrated how simple Google queries reveal the Achilles heel of a typical infrastructure networks -- default passwords and user accounts.
"SCADA is awesome at leaving default passwords because for some reason SCADA devices don't need to have strong passwords like every other system these days," he said.
He said that the SCADA software industry was years behind Microsoft fixing basic security holes, such as buffer overflows that would allow a malicious hacker to control a system. Grzelak has written tools to scan these networks for security gaps, which he hoped to commercialise to show clients how to protect their systems from infiltrators.
Simple precautions such as changing default network ports and suspect programming code would go some way to alleviating the danger, he said, although that may paradoxically void some manufacturers' warranties.
"The industry doesn't know much about the attacks that are possible," he said.
Smart meter risks
The session before Grzelak's was on smart energy meters that must be deployed across Australia and in Victoria before 2013. Consultant with IT company CSC, Gabriel d'Eustachio, said they offered great environmental benefits because consumers would have to "feel the pain" of rising spot prices for electricity generation and distribution through the day.
Energy distributors are looking at how to link these devices with public radio networks and possibly the national broadband network. But in d'Eustachio's opinion, the Federal Government's NBN won't be switched on in time.
Distributors and retailers would control devices in homes and offices, to switch them off or reduce their energy at will, he said. But attending risks include hackers infiltrating the system to take control of devices or capitalising on the habits of householders and businesses for their own aims.
But the biggest threats were householders who may be tempted to tamper with the devices to reduce their own energy bills or shunt them on to their neighbours, he said.
He said such risks were a "huge concern" to energy suppliers: "What happens if the guy who installs meters puts them on other people's houses?"
But the technology was queried by keynote presenter Steven Bellovin (pictured top), who said there were big question marks over how it was accessed by a third party and the communications protected and authenticated.
"How is that (electricity provider's) site protected?" Professor Bellovin asked.
"Someone can poll the thermostat in my house to see if I'm away on vacation? How do I know they can't?
"Or turn my thermostat off when I go away in winter and let my pipes freeze.
"Talk about overflow attacks."
The AusCERT Conference at the Royal Pines hotel on the Gold Coast runs to Wednesday.
Twitter feed from AusCERT is @natecochrane.







.jpg&h=140&w=231&c=1&s=0)








.png&w=120&c=1&s=0) iTnews Cloud Covered Breakfast Summit
iTnews Cloud Covered Breakfast Summit
 iTnews State of Security Breakfast
iTnews State of Security Breakfast
 iTnews State of Data & AI Breakfast
iTnews State of Data & AI Breakfast
 The 2026 iAwards
The 2026 iAwards
.jpg&w=120&c=1&s=0) Integrate 2026
Integrate 2026












_(1).jpg&h=140&w=231&c=1&s=0)



